约 300 字
1 分钟
杂项
摘要
该文本包含多个部分,包括代码、密钥和图像文件。其中一个部分是一个JavaScript函数`sgcc()”,该函数包含一个条件语句和一个alert函数。另一个部分是一个RSA私钥,用于加密和解密数据。还有一些图像文件和文本文件,包括一个名为“flag.txt”的文件,内容为一串数字。最后,文本中提到了一个Python脚本,用于破解一个MD5哈希值。总的来说,该文本似乎与密码学和安全相关。
bash
9
45
46
47
flag.txt
c=1566077545968868311749088444723100549024925747577903610033503
bash
内存镜像
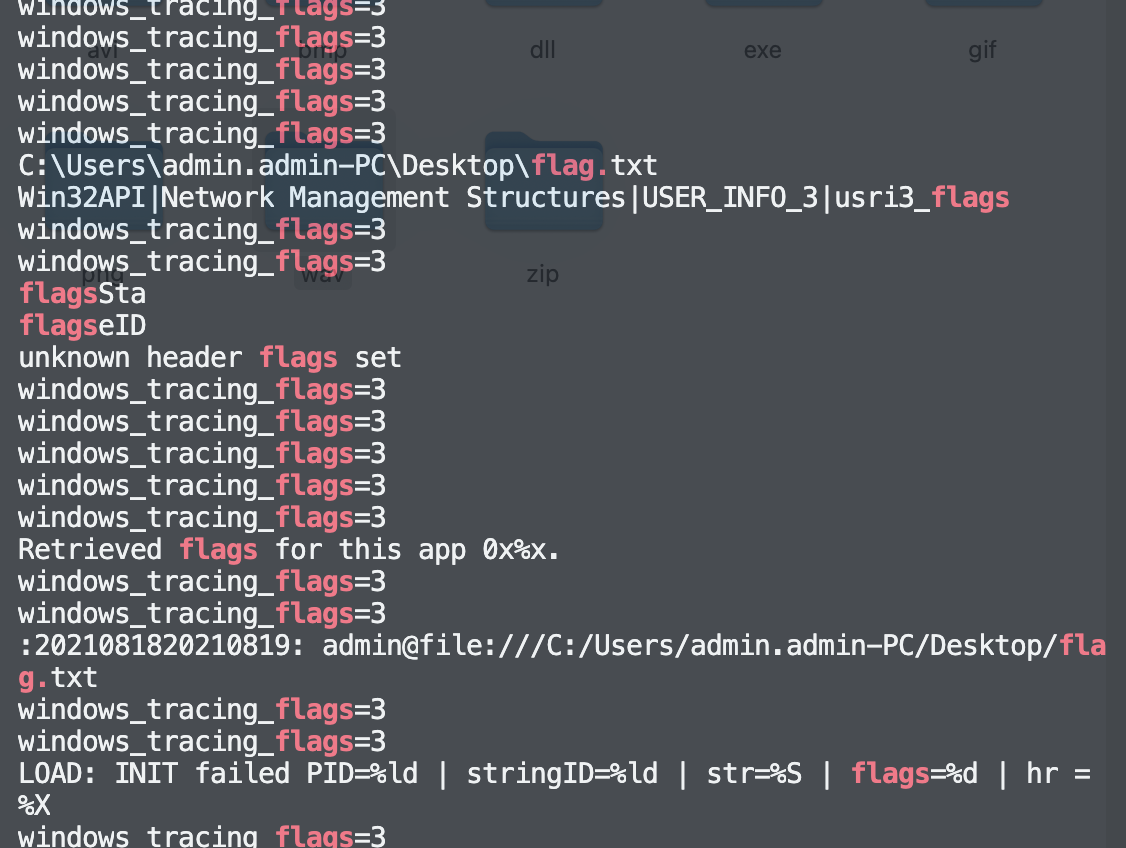
strings
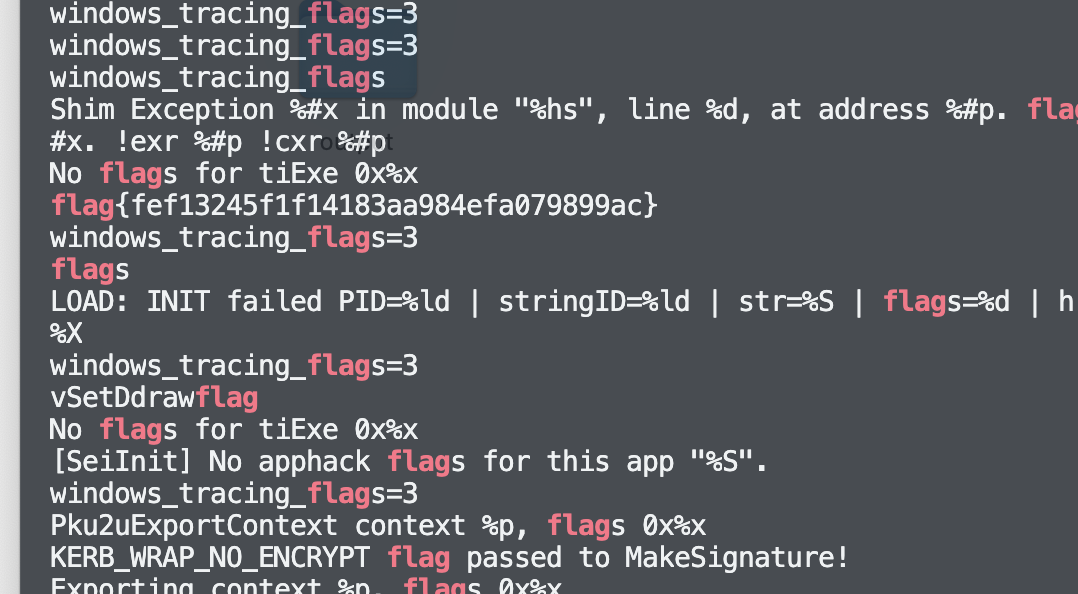
flag{fef13245f1f14183aa984efa079899ac}
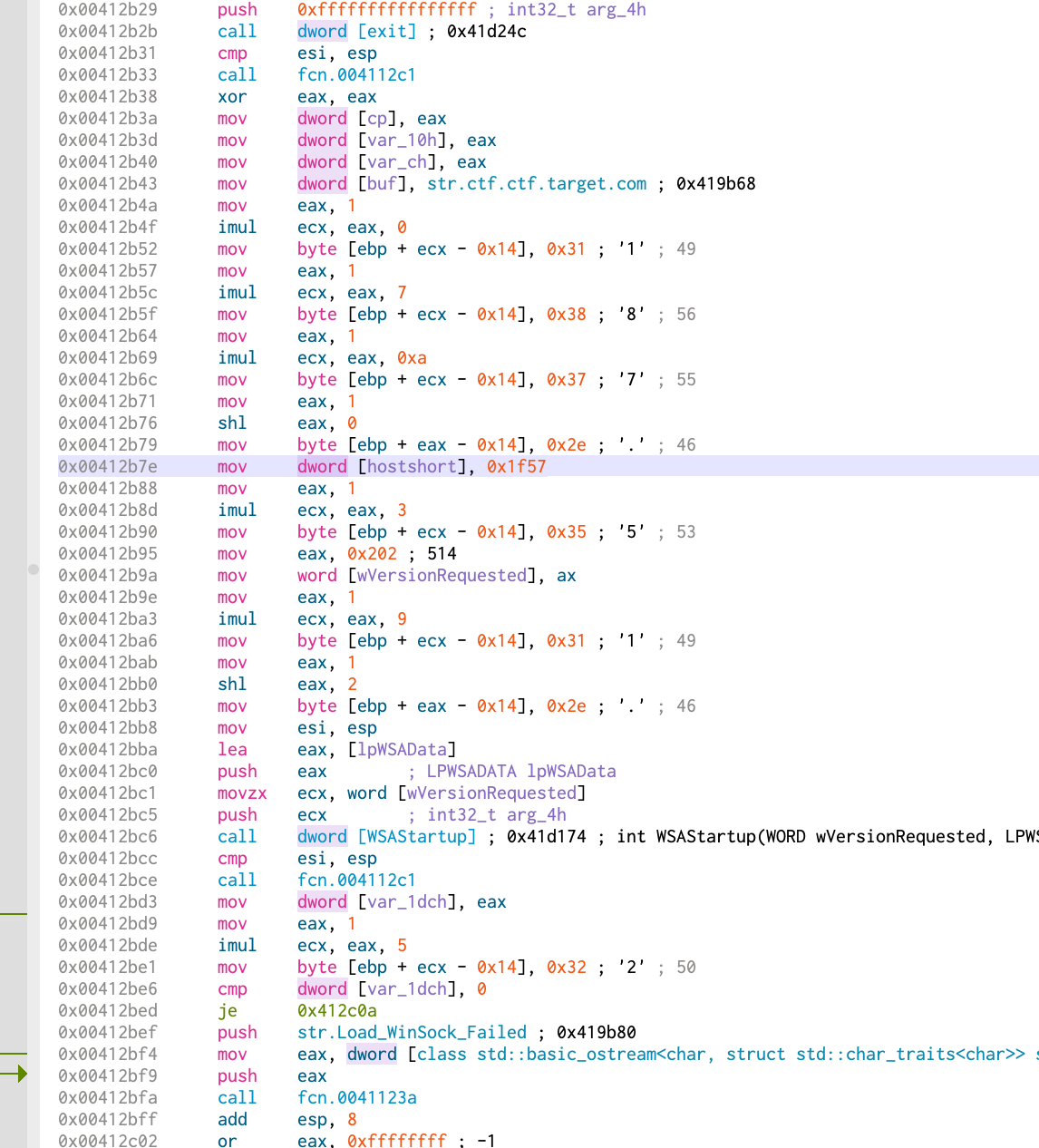
恶意文件
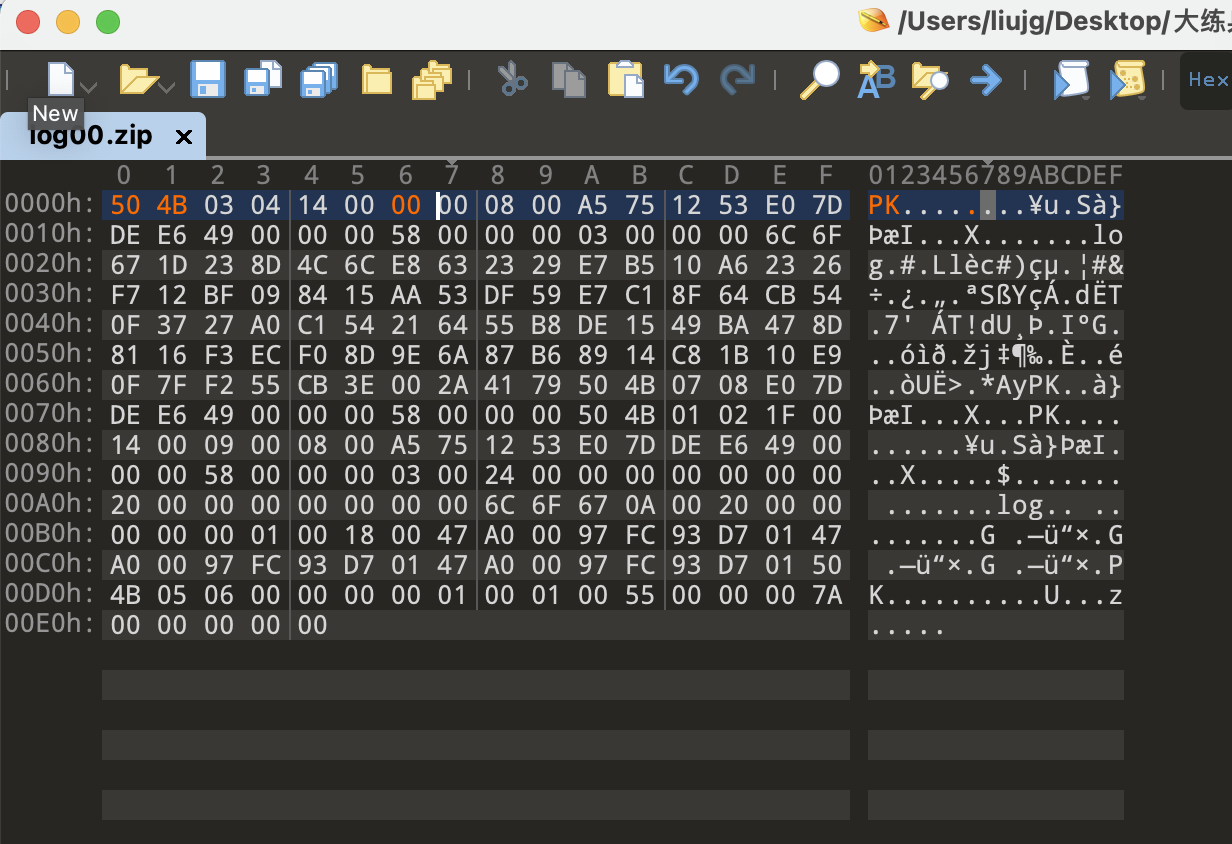
还是od比较快准狠
文件格式分析
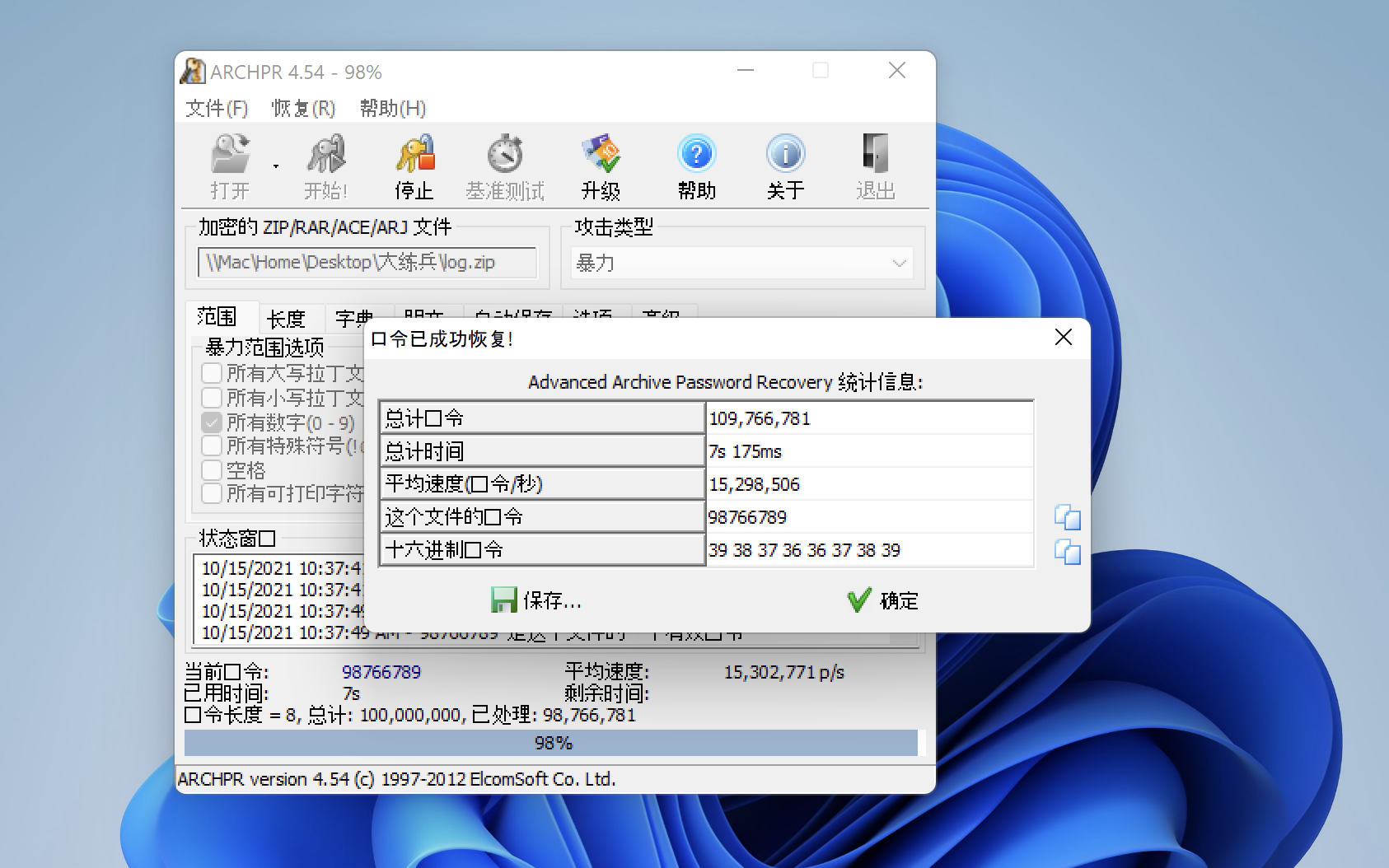
秘闻破解
bash
漏洞挖掘
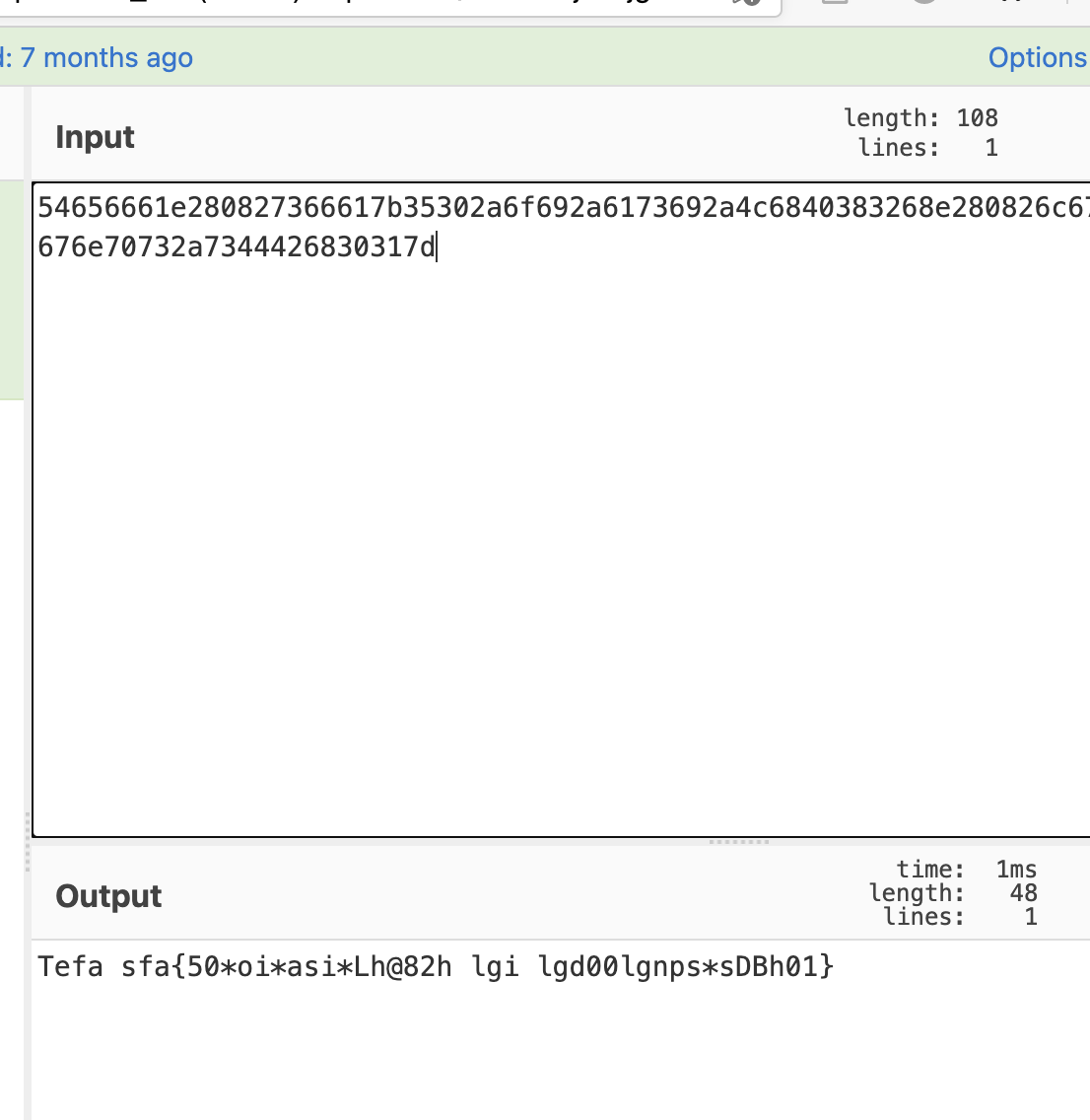
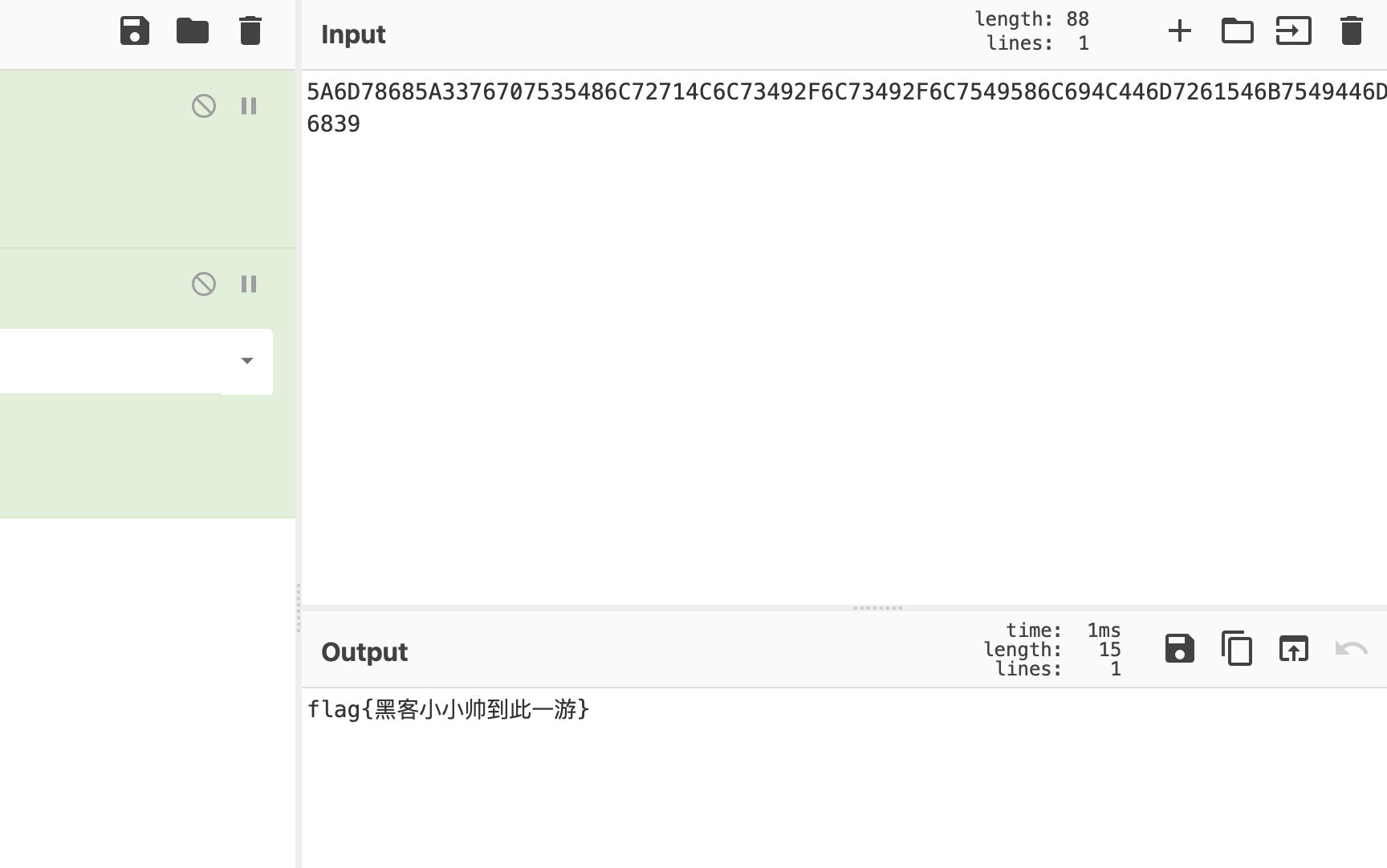
Tefa sfa{50_oi_asi_Lh@82h lgi lgd00lgnps_sDBh01}
栅栏
flag{d5000_login_pass_is_DLBhh@0812}
相关文章
暂无相关文章
